A new report from the Cyber Defence Centre at Ontinue has found a campaign targeting software developers with fake installation pages that look like official sites for AI tools like Claude Code.
The attack begins when a user searches for ‘install Claude code’ and clicks on a sponsored result. This link goes to a lookalike page that shows an installation command. While the real command uses the host ‘claude.ai,’ the fake version uses ‘events.msft23.com.’
Running this command enables Invoke-RestMethod to download a 600 KB, heavily obfuscated PowerShell script. This loader first checks the Windows region settings and stops immediately if the host is located in countries like Russia, Iran, or Ukraine.
But, if the location is not on the list, the malware searches for Chromium-family browsers, including Chrome, Edge, Brave, Vivaldi, Perplexity Comet, Helium, Arc, and Opera, to steal the v20 app_bound_encrypted_key and the v10 encrypted_key, which are keys used to lock browser data.
Exploiting the Elevation Service
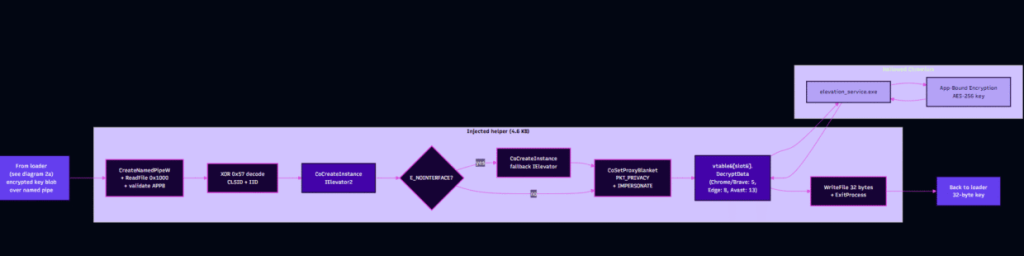
To bypass Google’s Application-Bound Encryption (ABE), the loader uses a native helper called payload_x64.bin. This is a small file compiled on 24 March 2026. It is injected into a live browser process through process hollowing. This is a method where hackers start a legitimate program, pause it, and then replace the real code inside its memory with their own malicious instructions to make the attack appear as a normal system process.
The helper uses the IElevator2 COM interface to ask the browser’s Elevation Service to decrypt the data. Ontinue researchers observed that the hackers are very quick to adapt as they added support for the IElevator2 interface within sixty days of the Chrome 144 release.
An Unusual Mistake
An interesting finding is that the hackers made a typing error in the code for Microsoft Edge. Researchers noted they used the number 4740 instead of 4047 in the interface identifier, which makes the first attempt fail on Edge 144. However, the malware simply falls back to the older IElevator interface that still works.
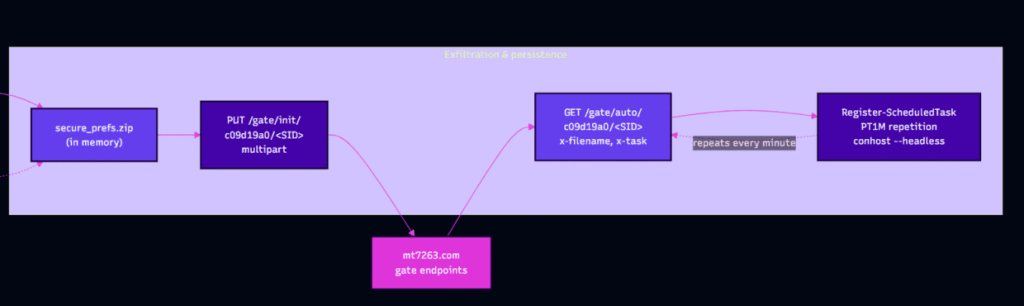
Once the 32-byte key is recovered, the PowerShell loader decrypts cookies, passwords, and payment methods from the browser’s SQLite databases and then creates a file called secure_prefs.zip in memory. This file is then sent to a server at mt7263.com.
The malware also sets up a Windows scheduled task to run every minute. This task uses conhost –headless PowerShell to check the server for new instructions.
Researchers stated in the blog post that this specific payload doesn’t match known malware families like Lumma or Glove Stealer.
“The sample documents a maintained, productization-shaped operation that is so far missing from public family taxonomy,” they explained.
Ontinue suggests that defenders should use PowerShell Script Block Logging and monitor for any unusual COM calls to stop these attacks before they can steal private data.
Industry expert insights
Commenting on the discovery, experts shared their views with Hackread.com regarding the dangers of targeting tech workers.
Vineeta Sangaraju, AI Research Engineer at Black Duck, noted that developers are high-value targets because they “hold the keys to an organization’s most sensitive assets.” She explained that “one compromised developer workstation does not stay contained,” as it allows hackers to move into source code and cloud environments.
Sangaraju warned that this campaign is particularly dangerous because it is “deliberately structured to look benign to scanners” and “actively evolving to stay ahead.”
John Gallagher, Vice President of Viakoo Labs at Viakoo, added that the ability to steal credentials has a high impact, especially for those managing large fleets of devices. “If a technician’s workstation is compromised by this ‘Claude Code’ stealer, the attacker gains the decrypted credentials used to manage the entire IoT fleet,” Gallagher said.
To limit the damage, he suggested that organizations should use “automated methods of rotating credentials” and focus on “agentless solutions” to remove the risk of malicious installers entirely.