Bitdefender Labs reveals how the China-linked FamousSparrow hacking group targeted an Azerbaijani energy firm using ProxyNotShell, Deed RAT, and Terndoor malware across three persistent waves.
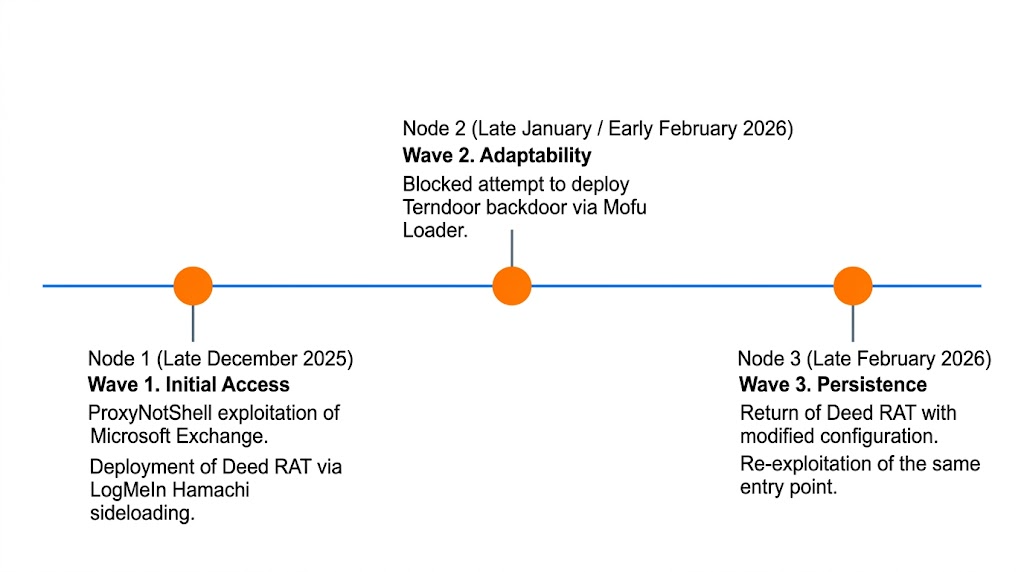
A new research report from Bitdefender Labs reveals a hacking campaign against an oil and gas firm in Azerbaijan, which was carried out in phases between December 2025 and February 2026. Researchers have attributed it to the China-aligned group FamousSparrow. The notable aspect of their research is the group’s sudden change in strategic interest, with the South Caucasus energy infrastructure becoming its latest target.
The Attack Cycle
According to research details shared by Bitdefender’s Martin Zugec, the campaign involved three distinct waves of activity, the first of which began on 25 December 2025. In this wave, the hackers used a vulnerability called ProxyNotShell to gain access to the company’s Microsoft Exchange server. To stay undetected, the group used a clever logic gate trick and managed to deliver the malware.
This involved DLL sideloading, where hackers tricked a legitimate program (LMIGuardianSvc.exe) into running a malicious file (lmiguardiandll.dll). This step activated the SNAPPYBEE (aka Deed RAT) backdoor, granting the attackers remote control.
Even when the firm attempted to clean its systems, the hackers exploited the same unpatched initial access vector three times in two months. This proves that removing malware is temporary if the original exploitation path remains open.
Gaining Deep Access
The second wave, detected in January 2026, introduced a tool called Terndoor. To bypass antivirus software, the hackers used the Mofu loader, an obfuscated stager that hid the malware’s instructions in the computer’s memory. Once activated, Terndoor installed a driver named vmflt.sys.
The hackers created a new service in the Windows registry (HKLMSYSTEMControlSet001Servicesvmflt) to establish a Rootkit and obtain deep, ‘god-mode’ control over the system. They then used the Impacket toolkit and Remote Desktop Protocol (RDP) to steal admin passwords. This helped them move laterally across the entire network.
Attackers’ Evolving Tactics
In late February, researchers recorded a third wave where the group deployed an updated version of Deed RAT. They shifted their files to a C:Recovery folder and used the address sentineloneprocom for communication.
This domain was likely chosen to mimic legitimate security traffic, making the malicious data look like a routine software update. This version hid inside standard Windows processes like SearchIndexer.exe and dwm.exe, using AES-CBC and RC4 encryption to lock away its configuration.
“Beyond the delivery mechanism, the operation is characterized by the deployment of two distinct backdoor families, Deed RAT and Terndoor, which were utilized across three separate waves of activity. This technical variety is matched by a strategic persistence, evidenced by the attackers’ repeated return to the same vulnerable Microsoft Exchange server entry point despite multiple remediation attempts,” researchers noted in the blog post shared with Hackread.com.
The key takeaway from this research is that determined hackers don’t just hit and run- they adapt and return. Bitdefender suggests that patching public-facing software like Exchange is the only way to stop this cycle, alongside consistent monitoring for API hooking, a technique where hackers intercept internal system conversations to maintain control.
(Photo by Zbynek Burival on Unsplash)