A new cybercrime campaign is turning supply chain attacks into a public competition, as TeamPCP and BreachForums operators launch a $1,000 contest that encourages hackers to compromise open-source packages.
The initiative, first highlighted by Dark Web Informer, signals an escalation in how threat actors are gamifying real-world attacks to recruit participants and expand their reach.
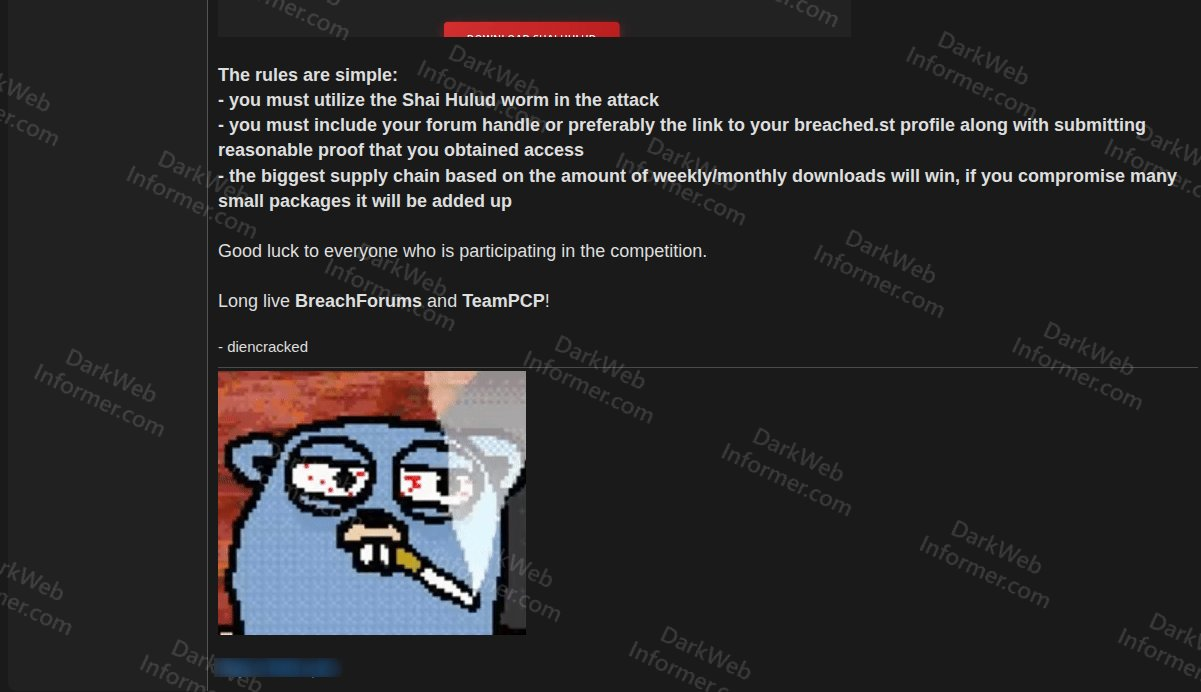
Participants are required to use a tool called “Shai-Hulud” to compromise open source packages and submit proof of access along with their forum identity.
The reward includes $1,000 in Monero, along with reputation points and recognition within the cybercrime community.
The contest introduces a scoring system based on download counts of compromised packages.
According to Dark Web Informer, the contest was announced on BreachForums by an account believed to be the forum’s owner in collaboration with TeamPCP.
Weekly and monthly download metrics determine the winner, meaning widely used packages offer higher scores. However, attackers can also combine multiple smaller compromises to boost their totals.
This approach encourages both targeted and broad attacks. Instead of focusing only on high-profile packages, participants are incentivized to compromise as many packages as possible across ecosystems.
In effect, the contest promotes widespread, indiscriminate infections rather than precision attacks.
Security researchers note that this model resembles worm-like behavior, where malicious code spreads rapidly across multiple entry points to maximize impact.
$1K Supply-Chain Attack Contest
Despite the dangerous implications, the financial reward is relatively small compared to the potential value of stolen access. A successful supply chain compromise can expose:
- CI/CD pipeline secrets.
- Cloud credentials.
- Maintainer tokens.
- Source code repositories.
- Enterprise environments.
Such access can be monetized far beyond $1,000, especially when sold to ransomware groups or access brokers. This has led analysts to believe the contest is less about profit and more about recruitment and visibility.
By offering a public leaderboard and recognition, TeamPCP is effectively attracting lower-tier or inexperienced actors willing to trade valuable access for status.
Adding to the threat, TeamPCP has released the Shai-Hulud attack tool as open-source malware, hosted on BreachForums infrastructure. A copy briefly appeared on GitHub before being removed, according to reports from users tracking the repository on X.
The availability of such tooling lowers the barrier to entry, allowing less skilled attackers to participate in supply chain attacks that previously required advanced capabilities.
TeamPCP has already built a reputation for targeting critical developer infrastructure. Research from Socket shows the group actively compromising platforms such as npm, PyPI, GitHub Actions, Docker images, and OpenVSX extensions.
Their strategy focuses on infiltrating tools that already operate within trusted environments. Once inside, they harvest credentials and enable downstream attacks across enterprise systems.
In earlier statements, the group openly mocked security vendors, claiming modern defenses are ineffective against their techniques.
The contest appears to extend an existing pipeline where stolen credentials are passed to other threat actors.
Previous campaigns linked to TeamPCP have reportedly impacted sectors including AI development, manufacturing, financial services, and government cloud platforms.
There are also overlapping claims involving groups like Vect, ShinyHunters, and Lapsus$, making attribution difficult even when attacks originate from similar supply chain compromises.
While the $1,000 reward may not attract highly skilled operators, it significantly increases the likelihood of reckless attacks. The contest introduces a public incentive structure that encourages copycat behavior across open source ecosystems.
For maintainers and security teams already dealing with persistent supply chain threats, this development adds a new layer of pressure.
By turning attacks into a competitive game, TeamPCP is not just exploiting vulnerabilities it is actively expanding the pool of attackers targeting the software supply chain.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.