A massive fraud network called FEMITBOT uses Telegram Mini Apps and fake brand names like Apple, Disney, and the BBC to trick users into investment scams and downloading Android malware.
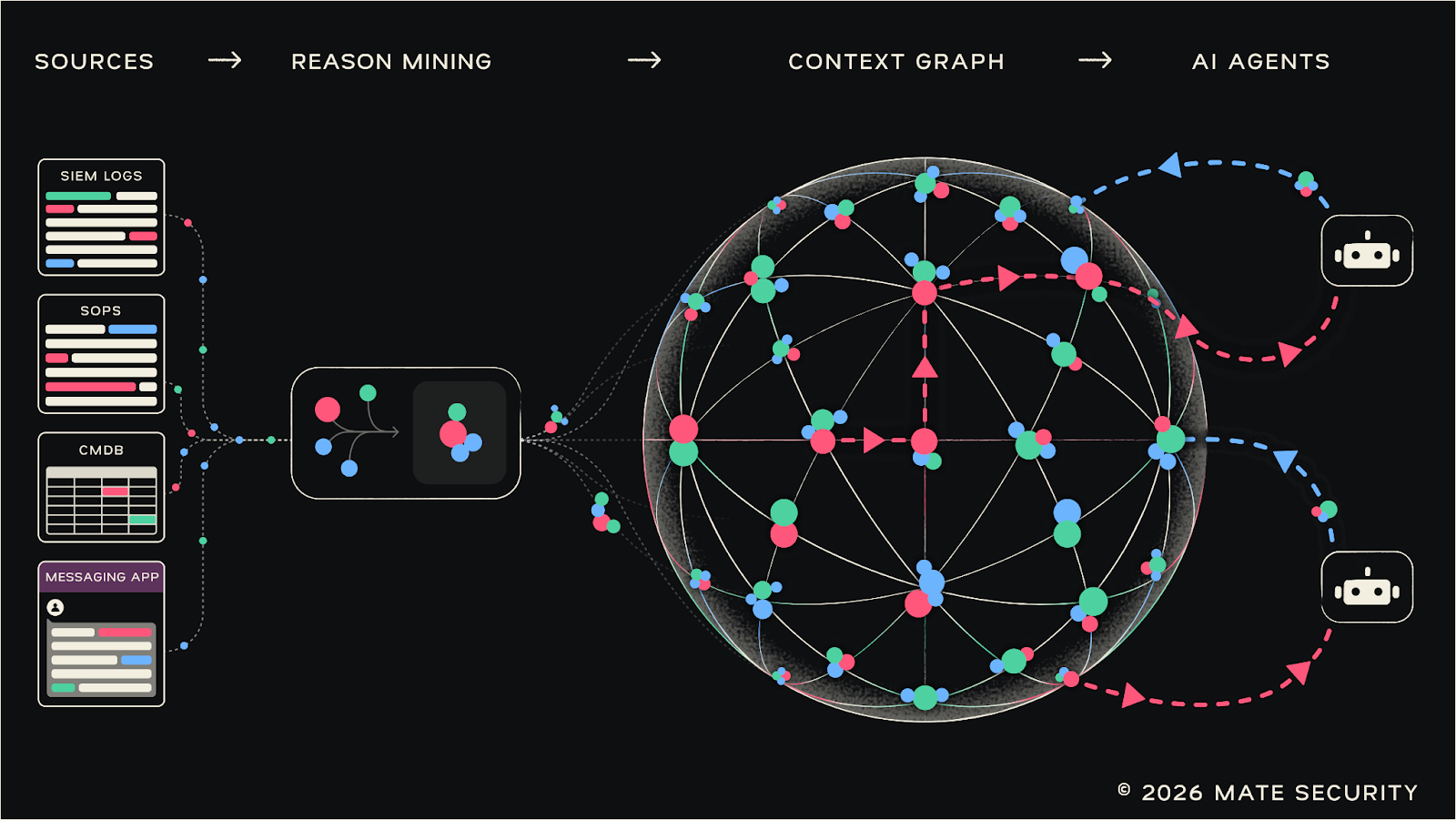
A massive fraud network, called FEMITBOT, is currently using Telegram’s Mini App feature to trick users into losing money and downloading malicious software in a new cryptocurrency scam wave. FEMITBOT is a centralized fraud infrastructure used by hackers to launch and manage hundreds of different scams at once.
This operation was discovered and named by the research firm CTM360 in a recently released report. They identified the name FEMITBOT after finding it hidden within the API responses (technical data sent from the hackers’ servers to the victims’ phones).
By using these built-in apps, the people behind the attack create a very smooth experience. It makes it hard for a regular person to tell they have actually left the secure parts of Telegram.
How the Scams Work
In this operation, the attackers use Telegram Mini Apps, which are lightweight programs that run inside the app’s own browser called WebView. When a user interacts with a bot and hits the Start button, these phishing pages pop up immediately. Since the page remains inside Telegram, it appears like it is a real part of the platform because it is not like a normal link that opens in Chrome or Safari.
The scammers use a few different ways to steal:
- Fake Dashboards: Users see screens showing fake earnings or high balances in cryptocurrency.
- Urgency: The apps use countdown timers and offers that expire in minutes. This forces people to make fast, panicky decisions.
- The Trap: To withdraw any earnings, the system says the user must first deposit their own money or refer friends. This is a classic lure used commonly in investment scams.
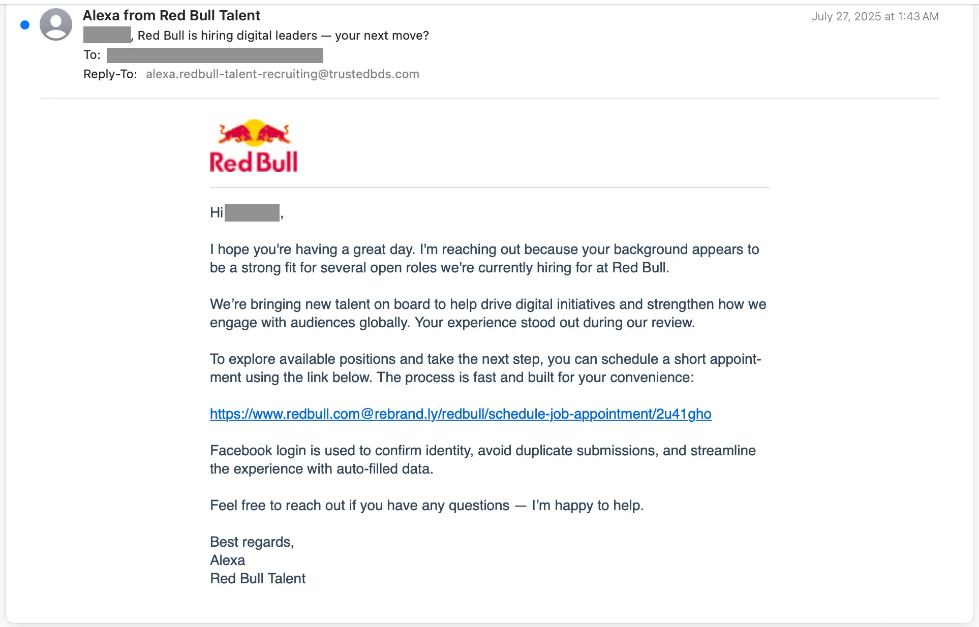
Brands and Dangerous Software
To appear legit, as per CTM360’s report, FEMITBOT copies global companies. They use logos and names like Apple, Disney, Coca-Cola, eBay, IBM, NVIDIA, MoonPay, and YouKu, as well as Binance and OKX. This makes the fake investment offers look like they are backed by giant, trusted businesses.
The operation also spreads Android malware, where some Mini Apps trick users into downloading APK files or installing Progressive Web Apps (PWAs). These malicious files impersonate apps from the BBC, NVIDIA, CineTV, Coreweave, and Claro. To stop phone browsers from showing security warnings, the attackers use TLS certificates. This helps the malicious files look safe and verified.
A Professional Setup
This isn’t just a small group since the entire network runs on a shared system, on which the hackers can change the branding or language of a scam almost instantly. Surprisingly, they even use marketing tools from Meta and TikTok, and also use tracking pixels to see which scams get the most clicks. It shows they are running this like a professional business. Be very careful with any bot that asks for a deposit before you can take your money out.
(Photo by Mohamed Nohassi on Unsplash)