- Business impersonation is the hidden thread connecting old and new fraud. Discover how the same core tactic is fueling both a surge in commercial check fraud and an explosion of AI-powered online shopping scams targeting younger consumers.
- Tools like Positive Pay and 3D Secure authentication, while effective against the fraud they were built to stop, have pushed threat actors to evolve their schemes in ways that render those controls irrelevant.
- Ecosystem gaps are often the real vulnerability. Fraudsters exploit the chain of assumed trust between social media platforms, card networks, merchant onboarders, banks, and local business registries — turning each party’s reliance on the last into an open door.
If you’re a millennial or Gen Z-er, then you probably haven’t used a paper check in a while. According to the Federal Reserve Bank of Atlanta, just 1 out of 5 of your peers used a check in the last 30 days, versus 2 out of 5 Gen Xers and 3 out of 5 boomers. Yet despite year-on-year decreases in overall usage, Nasdaq Verafin saw check fraud instances rise another 11% in 2025.
Then again, if you are a millennial or Gen Z-er, you will have seen an advertisement for a cheap product on social media. For 40% of you, that has meant falling for an online shopping scam.
On the face of it, these look like two ends of the fraud spectrum:
- On the one hand, we have what feels like the past: paper check usage rates even among those aged 65+ fell from 13% of transactions in 2013 to 6% in 2025 (Federal Reserve Bank of Atlanta).
- On the other hand, we have the future: online shopping scams target a younger demographic through AI-enabled brand impersonation and sprawling social media ad ecosystems.
The payment instruments, demographics, and the teams working at financial institutions to address these problems differ. So what’s the thread linking them together? Business impersonation. It manifests itself differently across schemes, but for anti-fraud systems built to detect check washing and counterfeiting on the one hand, and unauthorized third-party card fraud on the other, business impersonation has emerged as the fraudster’s response to exploit both.
Commercial checks and copycat businesses across state lines
In the past, stolen checks were often whitewashed to change the recipient and amount, and then walked into banks for cashout. The Postal Inspection Service received over 299,000 mail theft complaints in a single 12-month period—a 161% increase from the prior year. Recorded Future’s Fraud Intelligence Team analyzed and mapped stolen checks to US geographies, illustrating hot spots of physical crime and observing that it remains a national issue that extends beyond heavily urbanized areas.

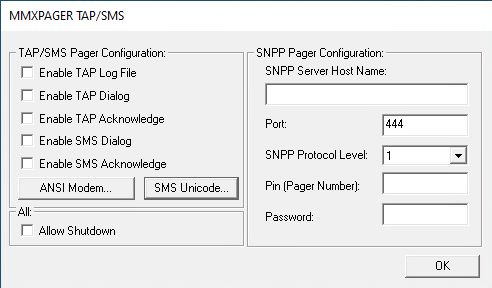
Mapping stolen checks by zip code; courtesy of Recorded Future
Yet even among declining consumer check usage rates, businesses’ use of commercial checks remains stubbornly high in the US: the Association for Financial Professionals (AFP) found that 91% of organizations are still using checks, and 63% experienced check fraud in 2024. When businesses send checks to suppliers, the amounts can rise quickly, leading fraudsters to expand beyond simple check-washing schemes.
In perhaps the most eye-catching example, fraudsters intercepted a commercial check destined for bubble-gum giant Bazooka in 2022. A $1.24 million check. Over the next two weeks, they transferred and withdrew over half a million dollars. How’d they do it? You can’t just wash out the payee name on a million-dollar check, replace it with John Smith, and expect it to clear after depositing it into a personal checking account.
Instead, the threat actors just created a fake Bazooka. The real Bazooka is registered in Delaware under the name “The Bazooka Companies, LLC”, so culprits registered a fictitious company in New York under the name “The Bazooka Companies 1 Inc”. They then used the official business license to open a corporate bank account for the new fictitious business. From there, they used cashier checks, withdrawals, and transfers to personal accounts to cash out the funds.
Fast forward to today, and the scheme is still happening. Recent research from Recorded Future Payment Fraud Intelligence (PFI) surveyed stolen checks for sale on Telegram in Q4 2025 and found over 30 checks with a business as the payee, along with suspicious new entities registered in other states a few days later. The total face value of the checks amounted to $2M.
As with most fraud, this scheme’s emergence is based on:
- Exploiting ecosystem gaps between disparate parties: Businesses can have the same name as another when registered in different states. Pair that with most states’ limited mandate to investigate business registrations, and we’re left with the first gap:
“As long as the basic filing requirements are met, the office[s] may have little or no authority to question or reject a document submitted for filing or to verify information included in the filing” (National Association of Secretaries of State, September 2025)
When a fraudster approaches a bank to open a business bank account, the bank conducts its own due diligence. But the focus here is on money laundering threats and the legitimacy of documents and applicants. If the fraudsters are using a clean identity — synthetic or otherwise — then the bank won’t have a clear reason to reject the application just because a business called John’s Toilet Supply, LLC exists in another state.
- Delivering a reactionary counterpunch to effective fraud processes: Think of this as the cat-and-mouse game. Fraud defenders figure out how to stop one scheme, forcing fraudsters to innovate. In this case, Positive Pay has proven remarkably effective at preventing check washing and counterfeit checks (when parties agree to use it). Payee Positive Pay, in particular, allows the payer to make sure that when their checks are deposited, the check number, date, payee name, and amount match their files. But what happens if everything is correct, but a copycat payee deposits the check? Cases like Bazooka.
80% discount on shoes? How can you say no?
If we detour into e-commerce, we see a very similar dynamic play out, but at a staggeringly larger scale. The premise is simple: use AI to launch a fake online shop impersonating company A, B, or C, buy ad space on social media to drive traffic, pocket the proceeds, and launder the funds while customers wait for goods that never arrive.
The scheme works because 53% of consumers, and 76% of Gen Zers, now begin shopping journeys on social media, according to Salesforce’s 2025 report. The problem is that the journey is littered with traps: in November 2025, leaked internal documents from Meta claimed the “company shows its platforms’ users an estimated 15 billion ‘higher risk’ scam advertisements — those that show clear signs of being fraudulent — every day”. Industry reporting paints the same picture, with the Better Business Bureau finding online shopping scams as the most reported scam type and social media advertisements as the most common originator.


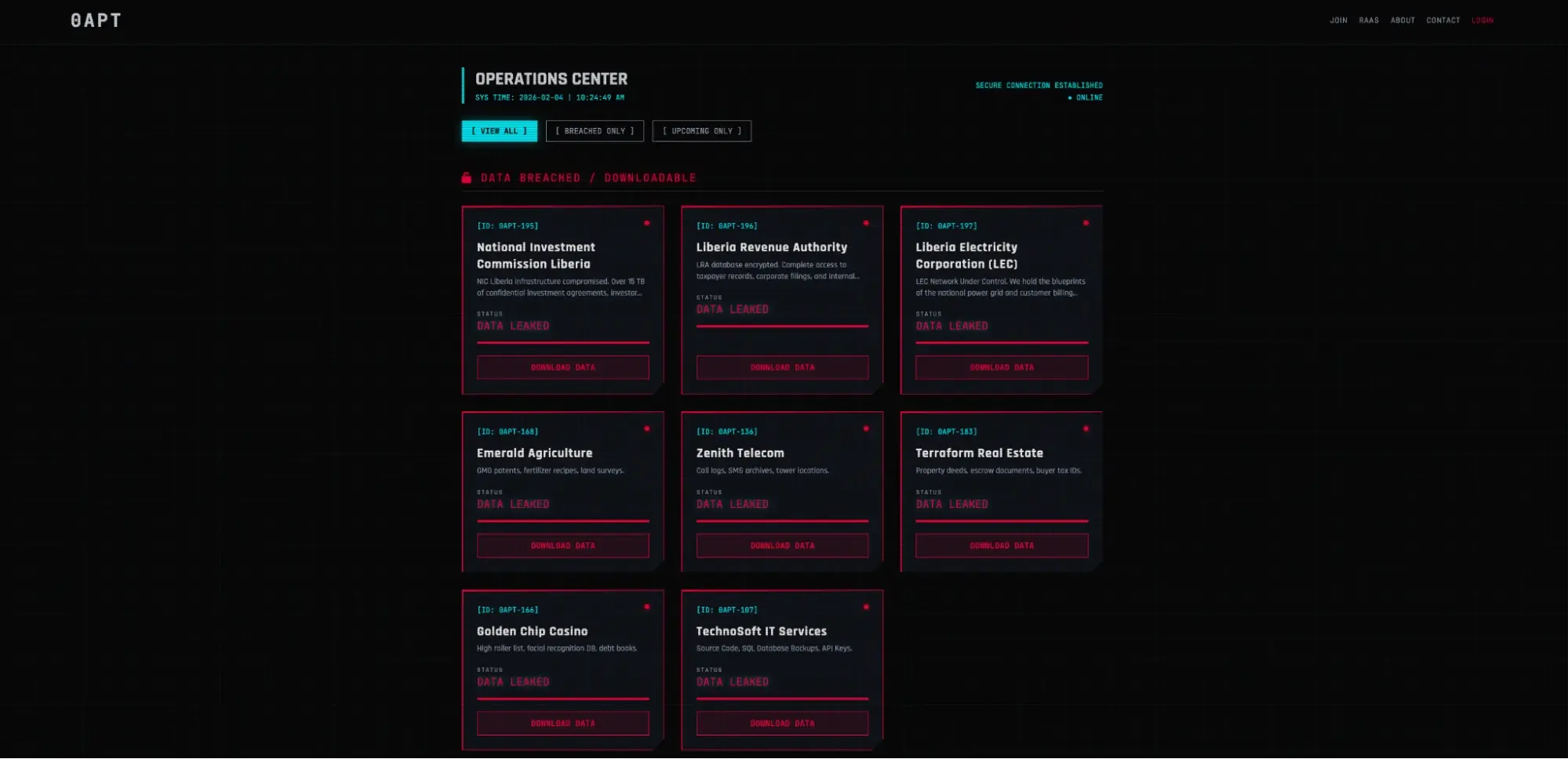
Brand impersonation shopping scams impacting shoppers in January 2026; courtesy of Recorded Future
The basics of the scheme are nothing new. Capture payment card data by creating a fake online store and advertise too-good-to-be discounts. What’s changed is that these are no longer just phishing websites. They’re functional online shops that process payments via merchant accounts. Behind each of these merchant accounts is a registered business.
This is creating problems throughout the ecosystem:
- Cardholders see websites that exactly mimic major (and increasingly niche) brands, letting discounts outweigh better judgment.
- Financial institutions face the challenge of balancing their duty of care to process customer transactions with the risks of fraud and money laundering. But in these cases, the traditional indicators of cyber-enabled fraud aren’t present. The cardholder is authorizing the transaction, and there’s nothing suspicious within the behavioral or device indicators of the 3D Secure authentication stream. (Because, again, it’s the cardholder doing the transacting under manipulation.)
- The fingers begin to point back at the acquirers and payment facilitators responsible for merchant onboarding, but, from their perspective, the entity holds a proper commercial license to engage in business issued by the local authorities. (Though, as a divergence from the check fraud scheme, the fraudsters in online shopping scams rarely impersonate a real big-name brand at the business creation and merchant onboarding stage. Instead, the fraudsters hide evidence of impersonation from the merchant onboarders and leave the impersonation for the ads and fake online shops visible to victims.)
But just like with the check fraud example, a big part of why online shopping scams have exploded — outside of generative AI making brand abuse content easier than ever to create at scale — is ecosystem gaps and fraudsters reacting to the defense:
- Exploiting ecosystem gaps between disparate parties: By the time a victim is making a purchase on an online shopping scam website, each entity along the way has looked to the one before and trusted that due diligence had been performed. The cardholder wants to trust that the social media platform screened out malicious advertisers; the card issuer wants to trust the cardholder vetted the merchant; the card network wants to trust the merchant onboarder verified the business; and the merchant onboarder wants to trust local authorities properly licensed the business. A big, long line of incentivized trust.
- Delivering a reactionary counterpunch to effective fraud processes: The industry has made huge strides in combating unauthorized, third-party card-not-present (CNP) fraud in the last decade. A major part of the success has been built on 3D Secure, introducing a layer of authentication on top of existing authorization controls. Online shopping scams completely sidestep the defensive layer by making the merchant the fraud surface and rendering cardholder authentication controls irrelevant.
Thinking towards the way out
On the check fraud side, the best solution may already be available, but, as with most solutions, it comes with trade-offs and adoption issues. The basic idea of Positive Pay and its derivative, Payee Positive Pay, is that a business informs its bank of the checks it is sending, and the bank only disburses funds if the check matches what the business provided. Positive Pay was designed to combat counterfeit and forged checks, and it does that very well.
Of course, in the Bazooka example of same-name business impersonation, this wouldn’t help. Nothing about the check was modified. So here, banks offer Reverse Positive Pay, which basically means the business personally signs off on each sent check. It can solve the problem but shifts more operational and investigatory expenses onto the business (which might explain why adoption rates are south of 20%, according to Datos Insights and Alkamai). In the end, though, it makes you wonder why not heed the advice and move to alternative electronic payment methods?
On the online shopping scam side, solutions are more complex and scattered across the ecosystem.
- At the top of the funnel, there’s rising pressure on online advertising platforms to do a better job at limiting the presence of fraudulent advertisements. Based on more leaked internal Meta documents, regulatory pressure may not be producing the desired outcome.
- At the merchant onboarding level, both the major card networks are forcing acquirers and payment facilitators to do more to defend the gates into payment processing, while also devoting more resources to identifying scam merchants that do make it in.
For card issuers on the frontline, it’s a more delicate dance. Card issuers aren’t on the hook for authorized card payments to fraudsters under the Fair Credit Billing Act (FCBA) or Electronic Funds Transfer Act (EFTA), but 67% of cardholders expect them to cover scam losses. Though when cards transacting on scam websites end up on the dark web for resale, and unauthorized charges start rolling in, it is the issuer’s problem.
The best solution aligns with the industry’s movement toward CTI-fusion models to address the cyber component of cyber-enabled fraud. The convergence of online shopping and purchase scams is precisely the type of problem the new organizational model was meant to combat.
In applying the CTI-fraud fusion model to purchase scams, traditional fraud assets start at the end of the fraud attack chain to correlate reported cardholder manipulation and non-delivery alerts against merchant account patterns. The CTI assets start at the beginning, sourcing online shopping scams at runtime and attributing the abused merchant accounts. The two teams then meet in the middle, using modeled transaction patterns and threat-hunted active scam websites, ultimately leading to the deployment of merchant-based fraud risk rules.
So, in the meantime, where does all this leave us? The same thing you’ve heard plenty of times: stop using checks if you can and don’t trust too-good-to-be-true offers from online ads.
How Recorded Future Helps
The research in this blog came directly from Recorded Future’s Fraud Intelligence teams. Two capabilities speak to the threats described.
- Payment Fraud Intelligence — tracks the complete fraud lifecycle: for check fraud, it uses OCR to extract payee, amount, and date from compromised checks being sold in forums, enabling deposit screening against known stolen checks; for card fraud, it monitors compromised merchants, stolen cards on criminal marketplaces, and the tester merchants fraudsters use to validate cards before striking.
- Digital Risk Protection — provides continuous monitoring across millions of sources for malicious sites, brand and executive impersonation, data leakage, and dark web mentions — with risk-based alerting that surfaces only actionable threats and takedown workflows built directly into the Platform.