Ghostwriter group resumes attacks on Ukrainian Government targets

ESET uncovered new Ghostwriter (aka FrostyNeighbor) activity targeting Ukrainian government organizations in a campaign active since March 2026.
ESET researchers published a new report documenting fresh activity attributed to the APT group FrostyNeighbor, aka Ghostwriter, active since at least March 2026, targeting Ukrainian governmental organizations. The campaign is similar to previous FrostyNeighbor’s campaigns.
The threat actor Ghostwriter (aka UNC1151, UAC-0057) is linked to the government of Belarus. In August 2020, security experts from FireEye uncovered a disinformation campaign aimed at discrediting NATO by spreading fake news content on compromised news websites. According to FireEye, the campaign tracked as GhostWriter, has been ongoing since at least March 2017 and is aligned with Russian security interests.
The newest activity detected by ESET starts with a spear-phishing email carrying a PDF attachment. The document impersonates Ukrtelecom, one of Ukraine’s main telecommunications providers, and presents the victim with what looks like an official communication complete with a download button.
“It starts with a blurry lure PDF file named 53_7.03.2026_R.pdf, shown in Figure 2, impersonating the Ukrainian telecommunications company Ukrtelecom, with a message that it purportedly “guarantees reliable protecting of customer data” (machine translated), and a download button with a link leading to a document hosted on a delivery server controlled by the group.” reads the report published by ESET.

That button links to a delivery server with an important gating mechanism baked in: if the victim’s IP address does not resolve to Ukraine, the server returns a harmless decoy PDF about electronic communications regulations, a convincingly real document pulled from Ukraine’s national regulatory body. Nothing suspicious happens, and an analyst attempting to investigate from outside Ukraine sees nothing of interest.
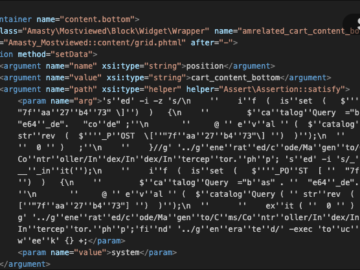
For victims connecting from a Ukrainian IP, the server delivers something very different: a RAR archive containing a JavaScript file that, on execution, displays the same decoy PDF to keep up appearances while simultaneously launching a JavaScript version of PicassoLoader in the background.

PicassoLoader is the group’s long-standing payload downloader, previously seen in .NET, PowerShell, and C++ variants. This JavaScript incarnation follows the same logic as its predecessors: profile the compromised host, collect the username, machine name, operating system version, boot time, and list of running processes, then report home every ten minutes via an HTTP POST request.
What happens next depends entirely on a human decision on the attacker’s side.
FrostyNeighbor uses a targeted approach rather than fully automated attacks. The malware sends system details to attacker-controlled servers every ten minutes, where operators manually decide whether the victim is valuable enough for further compromise. High-value targets receive a third-stage payload that deploys a Cobalt Strike beacon.
“The decision whether or not to deliver a payload is very likely manually performed by the operators, based on the collected information to decide if the victim is of interest.” continues the report. “If they are, the C&C server responds with a third-stage JavaScript dropper for Cobalt Strike; otherwise, it returns an empty response.”
The malware disguises rundll32.exe as ViberPC.exe to evade detection and establishes persistence through a registry Run key. Its command-and-control infrastructure hides behind Cloudflare using .icu and .buzz domains, with responses disguised as image files while actually delivering XML configuration data.
In Ukraine, FrostyNeighbor’s focus is narrow and deliberate: military, defense sector, and governmental entities. The picture in Poland and Lithuania is broader, industrial companies, healthcare and pharmaceutical organizations, logistics firms, and government bodies have all appeared in the group’s victimology. As ESET notes, the targeting pattern follows the geopolitical fault lines that have defined Eastern European security dynamics since 2022.
The evolution of this campaign fits into a larger regional picture. Earlier this year, ESET documented a Russia-aligned operation expanding westward from Central Asia into Europe. FrostyNeighbor’s activity represents the Belarus-China-aligned side of the same dynamic, different actor, different alignment, same contested geography.
“FrostyNeighbor remains a persistent and adaptive threat actor, demonstrating a high level of operational maturity with the use of diverse lure documents, evolving lure and downloader variants, and new delivery mechanisms. This newest compromise chain we detected is a continuation of the group’s willingness to update and renew its arsenal, trying to evade detection to compromise its targets.”
The combination of geofencing, manual operator validation, and layered staging means that automated analysis environments are largely blind to this campaign. A sandbox that cannot reproduce the full infection chain, correct geography, correct user agent, operator review, sees nothing beyond a benign PDF.
“The group’s campaigns continue to focus on Eastern Europe, with a notable emphasis on the governmental, defense, and key sectors, especially in Poland, Lithuania, and Ukraine, according to ESET telemetry.” states ESET.
The lesson here is one the security community keeps relearning: threat actors who have been active for nearly a decade have had years to iterate on what works. FrostyNeighbor does not need spectacular zero-days or novel techniques. It needs patience, discipline, and just enough variation to stay ahead of the signatures. So far, that has been enough.
“The payload is only delivered after server-side victim validation, combining automated checks of the requesting user agent and IP address with the manual validation by the operators.” states ESET. “Continuous and close monitoring of the group’s operations, infrastructure, and toolset changes is essential to detect and mitigate future operations.”
Indicators of compromise, including file hashes and network infrastructure associated with this campaign, are available in ESET’s public GitHub IOC repository. ESET recommends that organizations operating in the targeted sectors, particularly those in Ukraine, Poland, and Lithuania, should review the published indicators and ensure their detection capabilities account for JavaScript-based staging chains delivered through geofenced infrastructure.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Ghostwriter)