A threat actor infiltrated Grafana Labs’ GitHub environment, stealing a privileged token to download the company’s private codebase, and then attempted to extort the open-source observability giant with an unanswered ransom demand.
Grafana Labs disclosed on May 16, 2026, that an unauthorized party obtained a token granting access to its GitHub environment, enabling the threat actor to download its codebase.
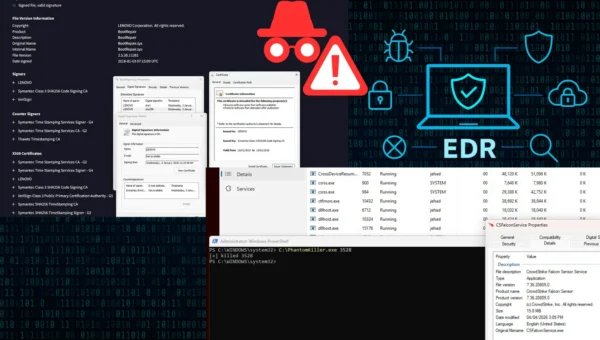
Grafana Labs Breach
The company confirmed the intrusion after one of its thousands of deployed canary tokens was triggered, immediately alerting the global security team.
The root cause was traced to a recently enabled GitHub Action that contained a “Pwn Request” vulnerability, a misconfiguration in a workflow triggered on pull_request_target events that granted external contributors access to production secrets during CI runs.
The attacker’s method was calculated and methodical. By forking a Grafana repository, injecting malicious code via a curl command, and dumping environment variables to a file encrypted with a private key, the threat actor successfully extracted privileged tokens.
The attacker then deleted their fork to cover their tracks before using the compromised credentials to replicate the attack against four additional private repositories.
After downloading Grafana’s private codebase, the attacker escalated the intrusion into extortion, demanding payment in exchange for not releasing the stolen code. Grafana Labs refused.
Citing the FBI’s published guidance that “paying a ransom doesn’t guarantee you or your organization will get any data back” and only “offers an incentive for others to get involved in this type of illegal activity,” the company determined that non-payment was the appropriate path forward.
The company stated its investigation has determined that no customer data or personal information was accessed during the incident, and that there is no evidence of impact to customer systems or operations.
Grafana’s security team moved swiftly to contain the breach. The compromised credentials were immediately invalidated, the vulnerable GitHub Action was removed, and all workflows across public repositories were disabled.
The incident has reignited community debate around CI/CD pipeline security and software supply chain risks.
Security researchers noted that the attack vector, a misconfigured pull_request_target workflow, is a widely underestimated attack surface across the open-source ecosystem.
The breach drew mixed reactions online: many praised Grafana for rapid transparency, while others wryly noted the irony of an observability-focused company missing alerts on its own infrastructure
Grafana Labs has confirmed to share additional findings from its post-incident review once investigations are complete, reinforcing its commitment to transparency with the developer and security communities.
Follow us on Google News, LinkedIn, and X to Get More Instant Updates.