Microsoft has revealed a stealthy intrusion campaign where attackers bypassed traditional malware and exploits, instead abusing trusted enterprise tools to silently infiltrate networks.
The technique highlights a growing shift in cyberattacks where adversaries rely on legitimate software and existing trust relationships to evade detection.
Notably, no vulnerability in HPE OA was exploited. Instead, threat actors gained access through a compromised third-party IT services provider responsible for managing the organization’s infrastructure.
This approach allowed attackers to operate entirely within normal administrative workflows. By executing scripts through HPE OA, their activity appeared indistinguishable from routine system operations, significantly delaying detection and response.
The attack aligns with MITRE ATT&CK technique T1199 (Trusted Relationship), where adversaries exploit existing business and operational trust paths.
In this case, that trust extended beyond the organization to an external service provider effectively expanding the attack surface.
According to Microsoft said in a report shared with GBhackers the attackers leveraged HPE Operations Agent (OA), a widely used and trusted IT management tool, to execute malicious actions across targeted environments.
On domain controllers, the attackers installed a malicious network provider named “mslogon,” enabling interception of user credentials during login and password changes.
Microsoft’s analysis shows the intrusion unfolded over several months. After gaining initial access, the attackers deployed VBScript payloads via HPE Operations Manager (HPOM), conducting network discovery and identifying Active Directory structures. From there, the campaign escalated into credential harvesting.
Microsoft Warns HPE Operations
The associated DLL captured usernames and passwords in cleartext and stored them locally, allowing attackers to reuse credentials for lateral movement.
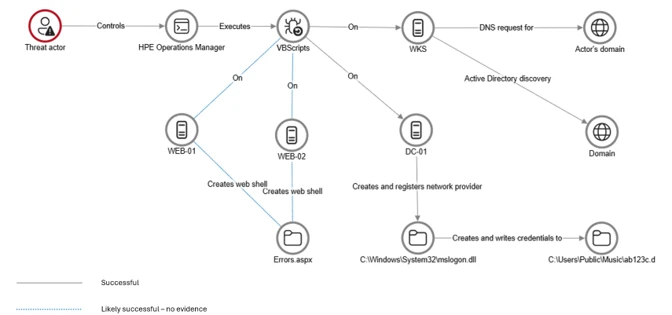
To deepen persistence, the attackers later deployed a second mechanism: a malicious password filter DLL called “passms.dll.”
This component integrated into the Windows Local Security Authority (LSA), capturing credentials whenever passwords were updated.
The stolen data was encoded and exfiltrated via SMB shares or disguised as image files, further blending malicious activity with legitimate traffic.
The captured data was not stored in cleartext. Instead, it was double encoded, first by using Base64, followed by a custom encoding routine embedded within the DLL.

In parallel, web shells were established on internet-facing servers, including modified application files such as “Signoff.aspx.” These web shells enabled remote command execution and file uploads while avoiding detection by mimicking normal application behavior.
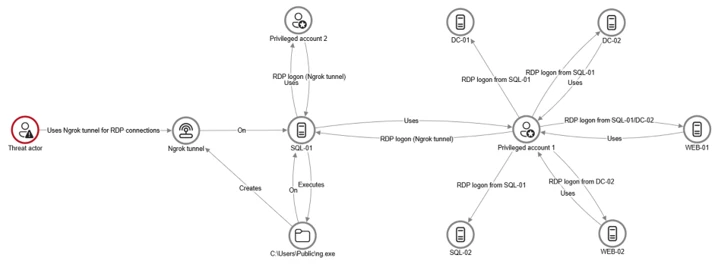
The attackers also deployed ngrok tunneling tools to maintain covert remote access. By creating encrypted tunnels, they enabled Remote Desktop Protocol (RDP) connections without exposing open ports, effectively bypassing perimeter defenses.
This allowed lateral movement across critical systems, including SQL servers and domain controllers.
Lateral movement was further supported by Windows Management Instrumentation (WMI)-based remote execution, which was used to deploy and launch ngrok on additional devices.
Despite multiple stages of compromise, the attack remained largely undetected due to its reliance on trusted tools, valid credentials, and legitimate system processes. Even after initial discovery, the threat actors reestablished persistence using previously compromised access points.
Microsoft emphasized that this campaign demonstrates a broader trend in modern cyber operations stealth over noise.
Rather than deploying malware that triggers alerts, attackers increasingly “live off the land,” abusing built-in tools and trusted relationships to maintain long-term access.
To defend against such threats, Microsoft recommends deploying endpoint detection and response (EDR) across all systems, enforcing strict outbound traffic controls, and enabling detailed logging on servers.
Organizations are also urged to adopt a zero-trust mindset, particularly when working with third-party providers, and continuously validate the behavior of trusted tools within their environment.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.