Gron Demo

Source link
Related Articles
All Mix →Severity Does Not Mean Priority
Table of Contents Discoverability: Hacker Findings Correlation Business Impact: Let Hackers Tell You Likelihood of Exploitation Planning Next Steps Automated scanners and tools are noisy;…
A Crazy Idea Regarding the Obama Administration and Security
I have a wicked crazy idea. What if we in the information security community were to organize a campaign to get level-headed, rational thinkers into…
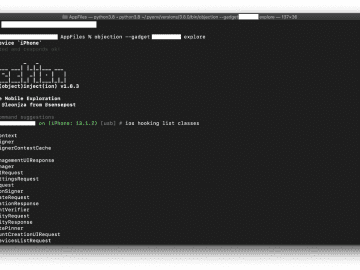
Low-Hanging Apples: Hunting Credentials and Secrets in iOS Apps
Diving straight into reverse-engineering iOS apps can be daunting and time-consuming. While wading into the binary can pay off greatly in the long run, it’s…
Unveiling the 5 hidden costs of a cyberattack
Table of Contents 5 hidden costs of a cyberattack 1. Financial losses 2. Disruption to operations 3. Damage to reputation 4. Compliance violations 5. Loss…
Your bug bounty journey, our priority
The foundation of a successful partnership is a shared commitment to mutual growth – this is something we firmly believe at Intigriti. That’s why when…
GDPR: Let’s kill the FUD
It seems everywhere you look, the talk about GDPR is designed to scare you into action. Fear, uncertainty, and doubt (FUD) are powerful motivators. Probably…