Hack the Box: How does linux work?

Source link
Related Articles
All Mix →How the Risk-Averse DoD Learned to Stop Worrying and Love the Hackers
There are few, if any, organizations more risk-averse than the U.S. Department of Defense. But even this staid agency has realized the security benefits of…
Meeting NIST API Security Guidelines with Wallarm
Table of Contents What is NIST SP 800-228? API Inventory and Discovery How Wallarm Can Help Request/Response Validation and Schema Enforcement How Wallarm Can Help…
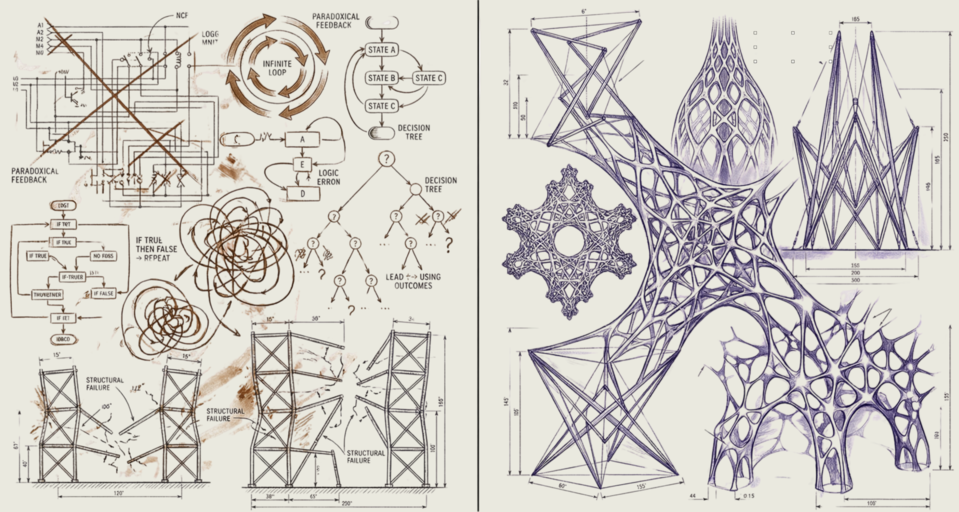
Bitter Lesson Engineering | Daniel Miessler
Table of Contents This is about more than just agentic engineering LIFE MANAGEMENT BUSINESS GENERAL AI INTERACTION My takeaways I have a new concept I’m…
The View from the Other Side: A Security Analyst’s Perspective on Bug Bounty Triage
Table of Contents Fact Check Reporting The Words of Motivation I was always intrigued about how things work on the other side of bug bounty. Well,…
Get Burp Suite certified for free… | Blog
Table of Contents How it works The offer What you'll need to prepare for the exam Ready for the challenge? Emma Stocks | 21 October…
Detectify releases API v2.5 – Detectify Blog
Security should be easy to integrate into the development cycle, which is why we offer our Detectify API integration for ease of managing your automated…