A sophisticated supply-chain attack has compromised the official distribution channel for DAEMON Tools, delivering multi-stage malware to users worldwide.
Since April 8, 2026, threat actors have distributed trojanized installers signed with legitimate digital certificates to conduct highly targeted cyberespionage operations.
Attackers successfully breached the development pipeline of AVB Disc Soft, the creators of the widely used DAEMON Tools software. They injected malicious code into software installers ranging from version 12.5.0.2421 to 12.5.0.2434.
The compromised executable files, such as DTHelper.exe, DTShellHlp.exe, and DiscSoftBusServiceLite.exe, carry valid developer signatures that allow the malware to evade basic security detections easily.
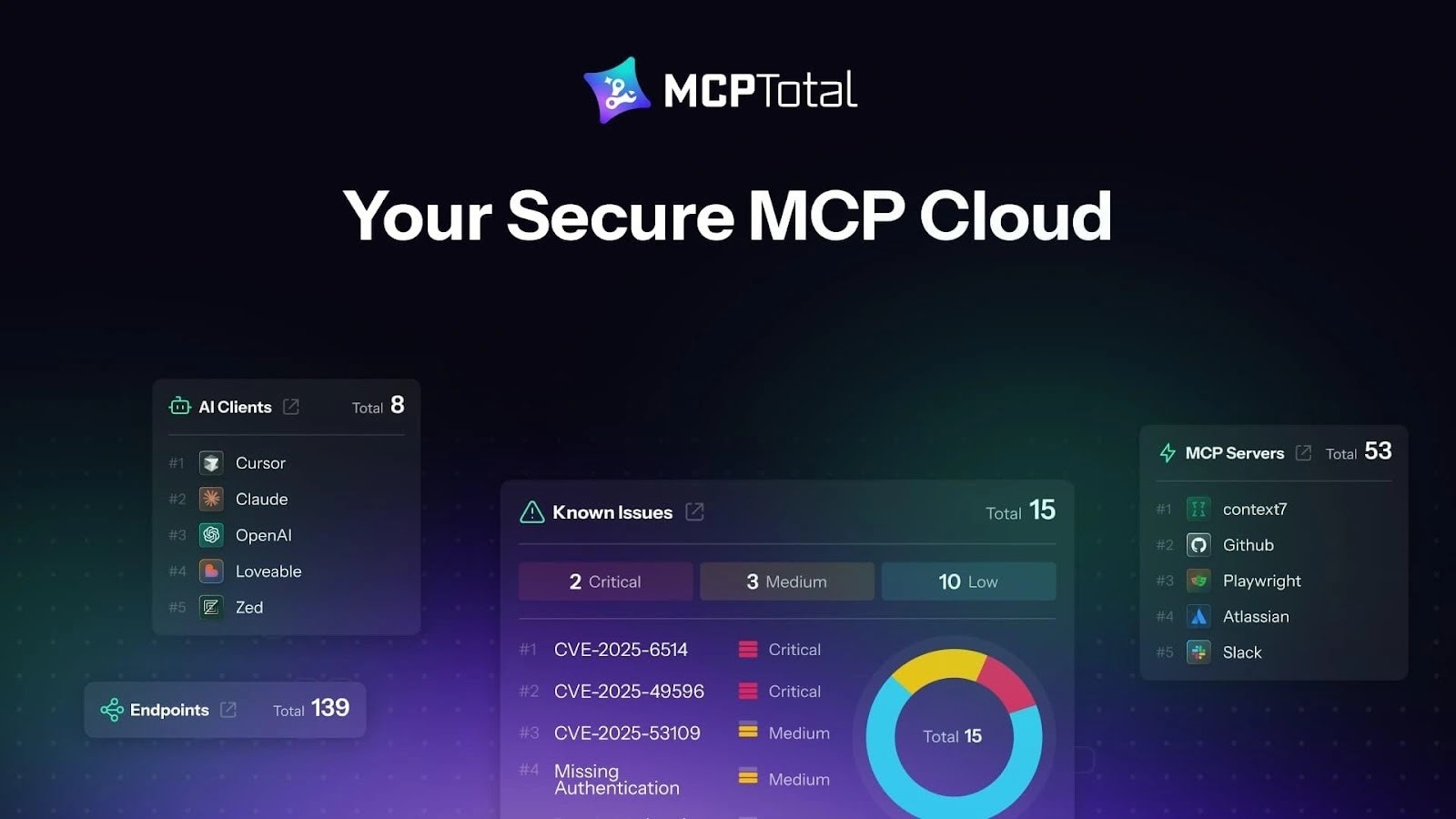
When a user launches the compromised application, a hidden backdoor within the startup code automatically contacts a typosquatted domain (env-check.daemontools[.]cc) to retrieve further malicious instructions.
Deep forensic analysis revealed that, for DAEMON Tools versions 12.5.0.2421 to 12.5.0.2434, the attackers successfully compromised three specific binaries within the software installations.
These files are DTHelper.exe, DiscSoftBusServiceLite.exe, and DTShellHlp.exe. These executables are typically located in the standard installation directory, such as C:Program FilesDAEMON Tools Lite.
Most dangerously, because these specific files are digitally signed by the legitimate developer, AVB Disc Soft, they easily bypass standard antivirus checks.
Whenever one of these binaries is launched, which typically happens automatically at machine startup, a hidden backdoor is activated. This backdoor is surgically implanted into the startup code that initializes the CRT environment.
It operates in a dedicated thread that sends GET requests to a malicious typosquatted domain: https://env-check.daemontools[.]cc. According to WHOIS records, the threat actors registered this domain on March 27, roughly a week before the supply chain attack began.
In response to the GET requests, the command-and-control (C2) server can return a shell command to be executed via the cmd.exe process. Security researchers from SecureList observed attackers using PowerShell commands to download and execute various executable payloads from remote servers secretly.
- Information Collector: The primary payload (envchk.exe) is a .NET executable deployed to gather system intelligence. It harvests the machine’s MAC address, hostname, DNS domain, running processes, and installed software to identify high-value targets. The code notably contains strings written in Chinese. However, security researchers have not yet definitively attributed the campaign to a specific advanced persistent threat (APT) group.
- Minimalistic Backdoor: Out of thousands of widespread infections, attackers manually deployed a secondary shellcode loader (cdg.exe) to roughly a dozen specific targets. This backdoor decrypts an RC4-encrypted payload directly in memory and communicates with command-and-control servers to execute arbitrary shell commands. Manual misspellings found in the deployment scripts (such as typing “chiper” instead of “cipher”) strongly indicate live, hands-on-keyboard activity by the hackers.
- QUIC RAT: The most advanced stage is a complex remote-access trojan dubbed QUIC RAT, which was deployed exclusively at a single educational institution in Russia. Written in C++ and heavily obfuscated with control flow flattening, it supports an array of communication protocols including QUIC, DNS, and HTTP/3. It maintains stealth by injecting malicious code directly into legitimate Windows processes, such as notepad.exe and conhost.exe.
The malicious update reached individuals and businesses in over 100 countries, with the highest concentration of victims located in Russia, Brazil, Turkey, Spain, Germany, France, Italy, and China.
While the initial profiling payload was distributed widely, the advanced backdoors were reserved exclusively for organizations operating in the retail, scientific, government, and manufacturing sectors.
Indicators of compromise
Infected DAEMON Tools Lite installers
9ccd769624de98eeeb12714ff1707ec4f5bf196d (12.5.0.2421)
50d47adb6dd45215c7cb4c68bae28b129ca09645 (12.5.0.2422)
0c1d3da9c7a651ba40b40e12d48ebd32b3f31820 (12.5.0.2423)
28b72576d67ae21d9587d782942628ea46dcc870 (12.5.0.2424)
46b90bf370e60d61075d3472828fdc0b85ab0492 (12.5.0.2430)
6325179f442e5b1a716580cd70dea644ac9ecd18 (12.5.0.2431)
bd8fbb5e6842df8683163adbd6a36136164eac58 (12.5.0.2433)
15ed5c3384e12fe4314ad6edbd1dcccf5ac1ee29 (12.5.0.2434)
Modified DiscSoftBusServiceLite.exe
524d2d92909eef80c406e87a0fc37d7bb4dadc14
427f1728682ebc7ffe3300fef67d0e3cb6b62948
8e7eb0f5ac60dd3b4a9474d2544348c3bda48045
00e2df8f42d14072e4385e500d4669ec783aa517
aea55e42c4436236278e5692d3dcbcbe5fe6ce0b
0456e2f5f56ec8ed16078941248e7cbba9f1c8eb
9a09ad7b7e9ff7a465aa1150541e231189911afb
8d435918d304fc38d54b104a13f2e33e8e598c82
64462f751788f529c1eb09023b26a47792ecdc54
C:WindowsTempenvchk.exe
2d4eb55b01f59c62c6de9aacba9b47267d398fe4
C:WindowsTempcdg.exe
C:WindowsTempimp.tmp
C:WindowsTemppiyu.exe
9dbfc23ebf36b3c0b56d2f93116abb32656c42e4
295ce86226b933e7262c2ce4b36bdd6c389aaaef
C2
env-check.daemontools[.]cc
38.180.107[.]76
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.