Hacking APIs: Fuzzing 101

Source link
Related Articles
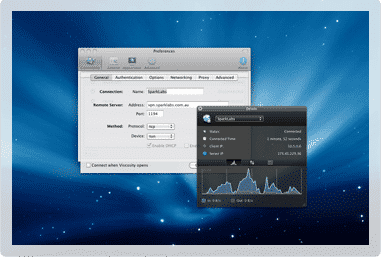
All Mix →How to Connect to an Astaro SSL VPN using OS X
I’ve been stupid for Astaro since the early 00’s and I remain so today. Today I run it in a virtual machine on an ESXi…
Octopus Strike! Three Argo CD API Exploits In Two Weeks
Argo CD is a popular Continuous Deployment tool that enables DevOps teams to manage their applications across multiple environments. However, in the past two weeks,…
Mac vs. PC Security In One Sentence
If you follow Information Security at all or have been part of a PC vs. Mac discussion at any level, you’ve probably come across the…
Finding security vulnerabilities with GitHub’s new code search
Finding security vulnerabilities with GitHub’s new code search Source link
Hacking for Good | HackerOne
We start the new year of 2020 with great prospects. First of all, 2019 turned out to be a massive success for hacker-powered security. HackerOne…
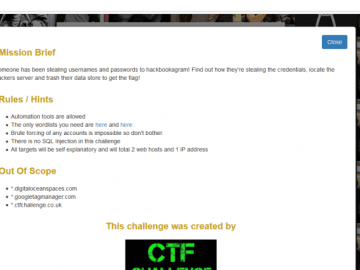
NahamCon – Trash the Cache Write-up (Web 1000)
I recently participated in the NahamCon CTF with the team Hacking for Soju. I was unable to complete this challenge before the end of the…