How some functions can be Dangerous | bin 0x01

Source link
Related Articles
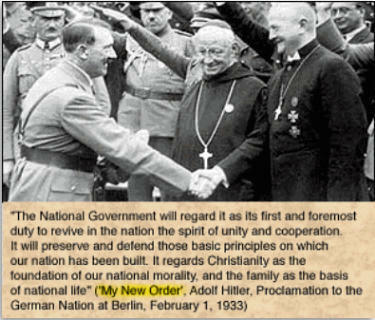
All Mix →Hitler, The Christian Warrior | Daniel Miessler
My feelings as a Christian points me to my Lord and Savior as a fighter. It points me to the man who once in loneliness,…
The future of pentesting is Human x AI, and it’s already in Burp Suite Professional | Blog
Table of Contents Key takeaways AI-assisted pentesting is the new normal Burp AI: Leading the human x AI wave Humans steer; AI accelerates The takeaway…
The Value of Elite Colleges is Relationships with Elite People
There’s been an unsolved mystery for a while that I want to solve in public. I didn’t solve it. It’s been solved. But few people…
WPA Key, WPA2, WPA3, and WEP Key: Wi-Fi security explained
Which one should you be using? Why Wi-Fi security matters. Setting up new Wi-Fi? Picking the type of password you need can seem like an…
HackerOne’s Digital First Workplace | HackerOne
Table of Contents How does HackerOne define a digital-first workplace? How did HackerOne become a digital-first workplace? How did HackerOne navigate the different pockets of…
Announcing HACK THE ARMY | HackerOne
Today, Secretary of the Army, Eric Fanning, announced plans to launch the U.S. Army’s first ever bug bounty challenge in partnership with HackerOne. The largest…