How They Got Hacked Episode Fifty 50

Source link
Related Articles
All Mix →8 High-impact Bugs and How HackerOne Customers Avoided a Breach: SQL Injection
This blog series counts down 8 high-impact vulnerability types, along with examples of how HackerOne helped avoid breaches associated with them. This blog, the third…
Meet the Hacker: Goonjeta Malhotra – “Hacking has always felt like a superpower”
Table of Contents TL/DR: Much like Darlene Alderson from Mr Robot, Goonjeta Malhotra entered the hacking battleground and sharpened her chops after taking inspiration from…
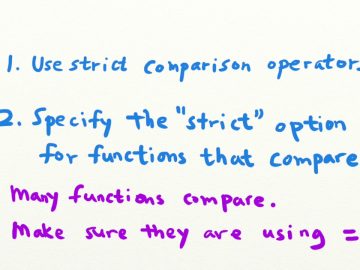
How to prevent PHP type juggling vulnerabilities
How to prevent PHP type juggling vulnerabilities Source link
InsertScript: MHTML: x-usc – A feature from the past
What is mhtml ? For those who have never saved a complete web page in Internet Explorer, mhtml or its extensions .mht is most likely…
Here’s how you can become member of my website.
My blog runs on Ghost. For some time it has a members feature. Last week I decided to enable it on my website. The reason?…
Bug Bytes #197 – In the Clouds
Bug Bytes is a weekly newsletter curated by members of the bug bounty community. The second series is curated by InsiderPhD. Every week, she keeps…