How They Got Hacked Episode Fifty Two 52

Source link
Related Articles
All Mix →Human Accomplishment: Engines vs. Fuels
I think a lot about why some people are highly productive and successful while others produce nothing in their lifetimes. Some get Ph.Ds and spend…
Efficient Security Principle (ESP)
One of the hardest things about being in information security is the frustration. The longer you’re in the field the more you’re exposed to ridiculously…
TomNomNom Demos a Ben Eater 8-bit CPU Emulator
TomNomNom Demos a Ben Eater 8-bit CPU Emulator Source link
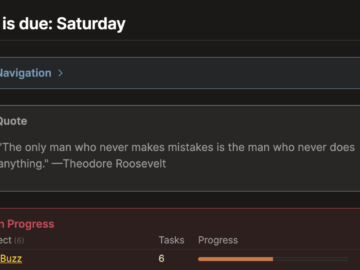
Simple, Focused, and Effective: Obsidian Daily Note Setup
.bh__table, .bh__table_header, .bh__table_cell { border: 1px solid #C0C0C0; } .bh__table_cell { padding: 5px; background-color: #FFFFFF; } .bh__table_cell p { color: #2D2D2D; font-family: ‘Helvetica’,Arial,sans-serif !important; overflow-wrap:…
Why The Valentine 1 Radar Detector Is Stupid
If you’re into cars, driving fast, or just technology in general you’ve likely heard of the Valentine 1 radar detector. It’s widely accepted to be…
HackerOne Live Hacking Event Recap: Denver 2022 (H1-303)
HackerOne Live Hacking Event Recap: Denver 2022 (H1-303) Source link