How To Pick Your Targets // How To Bug Bounty

Source link
Related Articles
All Mix →AI’s Threat to Newsletters – Daniel Miessler
We’re about to see a blast of AI-generated newsletters, and most human creators won’t survive Created/Updated: April 10, 2023 AI-driven newsletters are almost here. As…
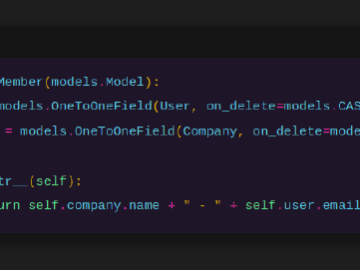
Writing efficient Django | victoria.dev
How to use Django’s views, models, and queries to build a better application. I like Django. It’s a well-considered and intuitive framework with a name…
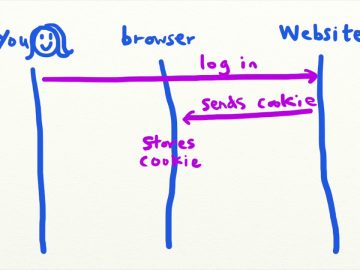
Intro to CSRF (Cross-Site Request Forgery) – Security Simplified
Intro to CSRF (Cross-Site Request Forgery) – Security Simplified Source link
The Three IT Roles: The King, the Sage, and the Cog
Table of Contents The King The Sage The Cog Which Are You? Life is Short I observe three basic types of people working in the…
Product Updates and Enhancements | HackerOne
Please find below a list of Feature updates/releases that happened in our first quarter! You can find more details about each one by going to…
Building a case for bug bounty programs
Table of Contents Dispelling doubts around ethical hackers 1. Aren’t we putting ourselves more at risk by opening ourselves up to hackers? 2. We’re not…