Free Hacking APIs Course (APISEC University!)

Source link
Related Articles
All Mix →TomNomNom Demos a Ben Eater 8-bit CPU Emulator
TomNomNom Demos a Ben Eater 8-bit CPU Emulator Source link
Cybernoz
1 min read
She Bought Me My Watch
Susan bought me my watch today. We walked into Tourneau (57th Ave, NYC) to check out some watches and we spent most of our time…
Cybernoz
1 min read
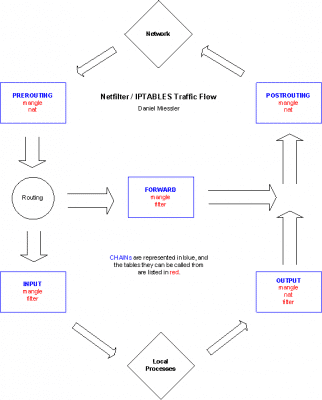
An IPTABLES Primer | Daniel Miessler
Table of Contents Stateful Packet Inspection Netfilter Basics TABLES CHAINS TARGETS How Packets Move Digging In "Passing Ports" Into A NATd Network Conclusion References iptables…
Cybernoz
7 min read
Black Friday and Cyber Monday price distortion identification
Table of Contents What is the impact of vulnerable validation systems? What are long and short-term fixes? How to identify currency confusion? The evolution of the internet and,…
Cybernoz
6 min read
Black Nannies Don’t Want To Work For Black Families?
From this NY Times article: It’s interesting that those middle class families that are complaining about unfair treatment don’t realize that they’re being judged according…
Cybernoz
1 min read