Email-borne worms are driving a fresh wave of incidents against industrial control systems (ICS), even as overall malware activity on these networks appears to be slowly declining.
New data from Q4 2025 shows that phishing-driven distribution of the XWorm backdoor has sharply shifted the risk landscape for operational technology (OT) environments worldwide.
The share of ICS computers on which malicious objects were blocked has been falling since early 2024, dropping to 19.7% in Q4 2025 the lowest level observed since 2022.
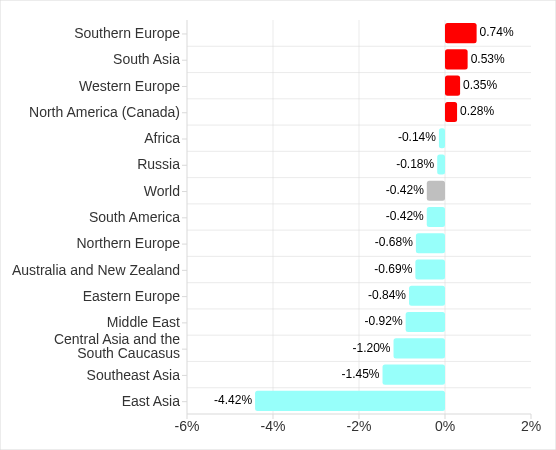
Regionally, the percentage of ICS systems with blocked malicious objects in Q4 2025 ranged from 8.5% in Northern Europe to 27.3% in Africa, underscoring persistent geographic inequality in OT security maturity.
According to the report, Over the past three years, this metric has decreased by a factor of 1.36, and by 1.25 since Q4 2023, suggesting a gradual hardening of many environments.
While most regions saw declines, four regions recorded increases, with Southern Europe and South Asia showing the most noticeable growth.
East Asia experienced a sharp spike in Q3 2025 due to the local spread of malicious scripts, but that indicator has since returned to typical levels.
Email-borne worm surge
The standout feature of Q4 2025 was a global rise in worms delivered via email attachments across all regions.
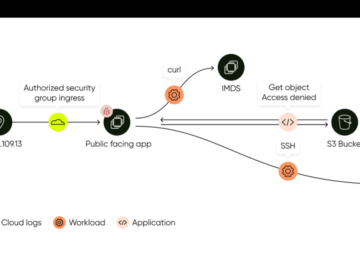
Much of this surge was tied to Backdoor.MSIL.XWorm, a worm-like backdoor designed to persist on infected systems and provide remote control capabilities to attackers.
Notably, this malware had not been observed on ICS computers in the previous quarter, yet it appeared simultaneously across all regions in Q4 2025.
Researchers link this sudden spread to a new obfuscation technique used in large-scale phishing campaigns collectively known since 2024 as “Curriculum-vitae-catalina.”
Adversaries targeted HR managers, recruiters, and hiring staff with emails masquerading as job applications, using subjects like “Resume” or “Attached Resume” and attaching a malicious executable typically named “Curriculum Vitae-Catalina.exe.” Once executed, the file infected the system and enabled remote access through XWorm.
The email-driven worm campaign unfolded in two waves during Q4 2025, peaking in October and November. Russia, Western Europe, South America, and North America (particularly Canada) were hit in October, followed by a blocking spike in other regions in November before activity subsided in December.
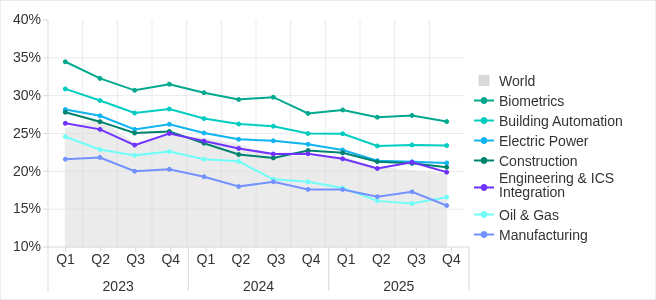
In Q4 2025, the share of ICS computers with blocked malicious objects increased in only one vertical: oil and gas, particularly in Russia, and Central Asia and the South Caucasus, though longer-term trends across all surveyed industries remain downward.
The highest percentages of ICS computers where Backdoor.MSIL.XWorm was blocked were seen in regions that have historically recorded high levels of email-borne threats on ICS systems: Southern Europe, South America, and the Middle East.
In Africa, where removable USB media remain widely used in industrial environments, XWorm was also detected when such devices were connected to ICS computers, indicating secondary propagation beyond email.
Overall, the percentage of ICS computers on which worms were blocked jumped 1.6-fold to 1.60% in Q4 2025, with Southern Europe showing the largest increase, up 2.16 times.
Industries, sources, and threat types
The biometrics sector continues to rank among the most exposed ICS-driven industries, due largely to broad internet accessibility of systems and weak cybersecurity controls at many consumer organizations.
The percentage of ICS computers on which malicious documents were blocked increased for three consecutive quarters. However, in Q4 2025 it decreased by 0.22 pp to 1.76%.
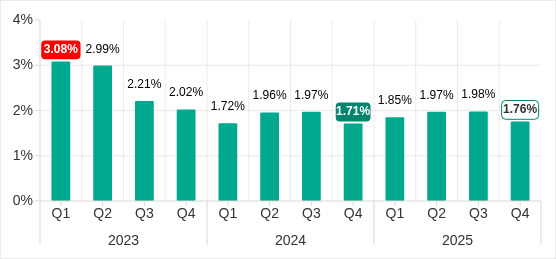
Across ICS environments, Kaspersky solutions blocked malware from 10,142 different families in Q4 2025, with only two categories worms and Windows-executable miners rising during the quarter.
The main threat sources remained the internet, email clients, and removable media, but by Q4 2025 the percentage of ICS computers hit from all sources except email had fallen to their lowest levels in three years.
Internet-borne threats dropped to 7.67% of ICS computers, while email-borne threats ranged from 0.64% of ICS machines in Northern Europe to 6.34% in Southern Europe, and removable-media threats ranged from 0.05% in Australia–New Zealand to 1.41% in Africa.
Initial infection vectors such as denylisted internet resources fell to 3.26% of ICS computers, the lowest level since 2022 and 1.8 times lower than Q2 2025.
Malicious scripts and phishing pages, however, still led all categories at 6.58% of ICS computers globally, with South Asia reaching 10.50% following a 3.47 percentage-point increase.
Next-stage malware (spyware at 3.80%, ransomware at 0.16%, and web miners at 0.24%) all declined, while Windows-based miner executables edged up to 0.60%, reinforcing that while broad exposure may be shrinking, targeted financially motivated attacks against industrial systems are becoming more specialized.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.