Malicious NuGet packages posing as legitimate developer utilities are targeting ASP.NET projects to steal identity credentials and silently backdoor applications through a localhost proxy.
All four were published between August 12–21, 2024, by a NuGet user named “hamzazaheer” and have collectively amassed a little over 4,500 downloads before takedown requests were submitted.
The campaign’s core objective is to intercept ASP.NET Identity authorization flows, exfiltrate user and permission data, and inject attacker-controlled authorization rules to create persistent backdoors in victim applications.
The lead package, NCryptYo, masquerades as a cryptography library through aggressive typosquatting of the legitimate NCrypto package while shipping an obfuscated dropper instead of real encryption routines.
Socket’s Threat Research Team has uncovered a coordinated NuGet supply chain attack abusing four interlinked packages – NCryptYo, DOMOAuth2_, IRAOAuth2.0, and SimpleWriter_ – to compromise ASP.NET web application developers.
Although it exposes a public API with Encrypt and Decrypt extension methods, every method returns null, while the true malicious logic is hidden behind JIT-time decryption and runtime hooks.
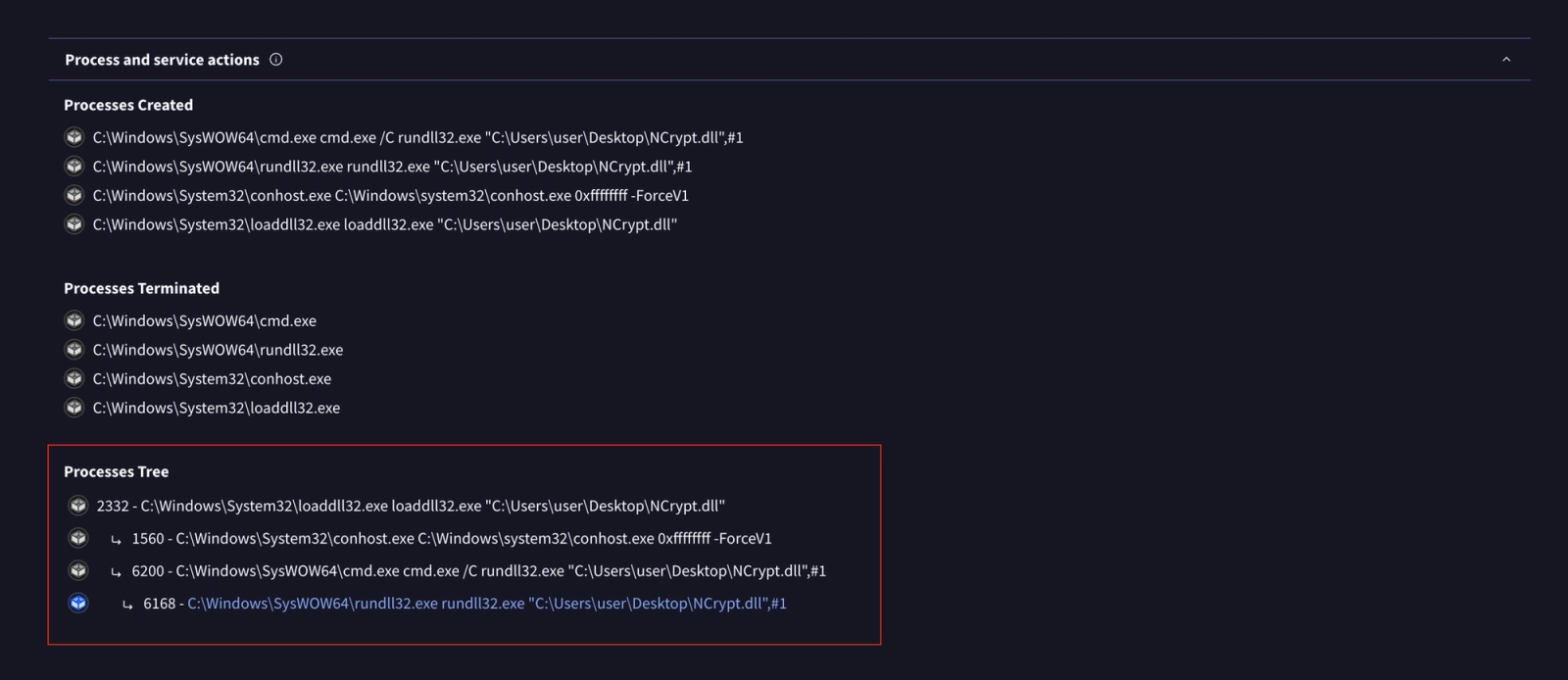
VirusTotal analysis reportedly shows only 1 of 72 vendors flagging NCrypt.dll as malicious, underscoring how heavily obfuscated .NET malware can evade conventional static detection.
JIT Hooking, Localhost Proxy
Once referenced in a project, NCryptYo’s static constructor executes on assembly load, installing JIT compiler hooks that decrypt embedded payloads and deploy a second-stage binary.
The package name targets NCrypto, the DLL filename NCrypt.dll mimics Windows’ CNG cryptography provider at C:\Windows\System32\NCrypt.dll, and the namespace NCrypt matches Microsoft’s cryptography APIs.
NCrypt.dll, highlighting the challenges of detecting heavily obfuscated .NET malware (Source : Socket’s Threat Research).This stage-2 component establishes a local proxy on https://localhost:7152, which becomes the pivot point between the malicious NuGet ecosystem and external command-and-control infrastructure whose address is resolved dynamically at runtime.
NCryptYo contains no visible networking code in its metadata, instead relying on this hidden payload and local tunnel to relay traffic for the companion packages.
DOMOAuth2_ and IRAOAuth2.0 plug directly into ASP.NET Identity flows to siphon sensitive authentication and authorization data.
DOMOAuth2_ integrates via an IServiceCollection extension that registers an internal OAuthService, then silently exfiltrates user GUIDs, role IDs, role mappings and module-level permissions whenever developers call methods like GetUserPermissions or UpdateRolePermissions.
All outbound requests are sent to https://localhost:7152/api/auth/ using a hardcoded attacker credential that is automatically applied when no API key is configured, and the token is hidden from typical JSON logging via JsonIgnore annotations.
VirusTotal sandbox results confirm this execution path, with process trees showing loaddll32.exe spawning cmd.exe which invokes rundll32.exe with the DLL.
IRAOAuth2.0 mirrors the same four exfiltration endpoints but removes all configurability, inlining the attacker’s auth token directly into each request and ignoring any caller-supplied AuthKey parameter.
Malicious NuGet Packages
This hardcoded-only channel ensures credential theft continues even if developers attempt to override or lock down DOMOAuth2_.
Both packages also support a bidirectional control path where the C2 server can return modified permission data, allowing the attacker to dynamically grant themselves elevated roles or alter access rules at runtime.
SimpleWriter_ rounds out the toolkit by adding unconditional file write and stealthy process execution capabilities under the guise of HTML-to-PDF conversion.
Each call to ConvertHtmlToPDF first beacons to the localhost proxy, then writes arbitrary content to disk and starts a hidden process (wkhtmltopdf.exe) with output streams redirected, regardless of network reachability.
The binary itself is not shipped in the package and is expected to be dropped by NCryptYo, giving the attacker flexible control over what actually executes on developer systems and, ultimately, in production environments.
By chaining these components, the threat actor focuses less on compromising developer endpoints directly and more on quietly weaponizing the applications those developers ship.
Once affected ASP.NET applications are deployed with these dependencies, the localhost proxy and C2 channel continue operating in production, streaming authorization data off-site and accepting attacker-supplied authorization rules that can grant admin-level access on demand.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.