A report by VulnCheck shows nation-state hackers often target flaws in aging routers, firewalls and VPNs.
Related Articles
All CyberSecurityDive →Financial services tech leaders tackle agentic AI governance
The proliferation of autonomous systems and tools is changing the risk management landscape for financial services companies, according to technology leaders speaking Thursday during the…
‘Shadow AI’ increases cost of data breaches, report finds
Listen to the article 3 min This audio is auto-generated. Please let us know if you have feedback. Dive Brief: Unmonitored artificial intelligence tools are…
Jaguar Land Rover begins phased restoration of services following cyberattack
Jaguar Land Rover said it has restored a portion of its digital operations as part of a controlled restart, weeks after a major cyberattack. The…
Nevada ransomware attack traced back to malware download by employee
An August ransomware attack against the state of Nevada has been traced to a May intrusion, when a state employee mistakenly downloaded a malware-laced tool…
Threat groups using AI to speed up and scale cyberattacks
Hackers are using ransomware to accelerate the timeline for cyberattacks, moving on average four times faster than just a year ago, according to an incident…
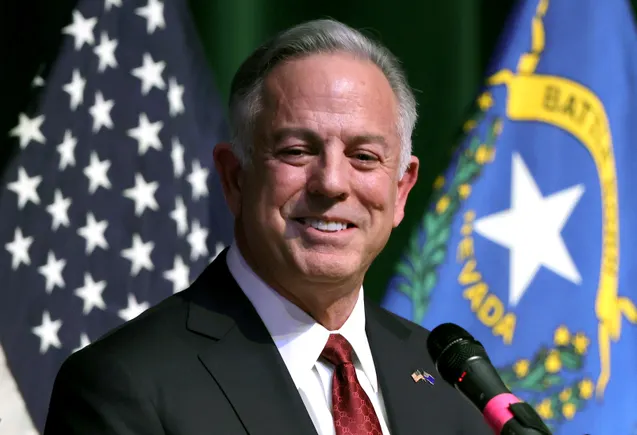
Gainsight CEO promises transparency as it responds to compromise of Salesforce integration
Gainsight CEO Chuck Ganapathi assured customers in a blog post published Tuesday that it was actively working with Salesforce and third-party forensic experts to respond to…