Salt Typhoon breach IBM subsidiary in Italy: a warning for Europe’s digital defenses

April 2026 breach at Sistemi Informativi (IBM Italy) raises concerns over Chinese-linked cyber ops in Europe, including Salt Typhoon.
In late April 2026, the Italian cybersecurity landscape was shaken by a significant breach targeting Sistemi Informativi, a company wholly owned by IBM Italy that provides IT infrastructure management for key public and private institutions. The incident, first reported by La Repubblica, has raised fresh concerns about the growing reach of Chinese-linked cyber operations in Europe.
Sistemi Informativi is central to Italy’s digital infrastructure, managing systems for public agencies and key industries. Its outage quickly raised alarms among cybersecurity authorities and critical infrastructure operators.
IBM confirmed the security breach through an official statement, acknowledging that it had “identified and contained a cybersecurity incident” and had activated incident response protocols involving both in-house and external specialists. The company said systems are now stable and services restored, but gave no details on the breach’s scope. Its website stayed offline for hours during containment.
While forensic investigations are still ongoing, multiple intelligence sources cited by La Repubblica point to the China-linked cyber espionage group Salt Typhoon. If confirmed, this would mark one of the most ambitious cyberattacks on the backbone of Italy’s public infrastructure in recent years.
Salt Typhoon has been active since at least 2019, but its operations have escalated sharply over the past two years. The group has built a reputation as one of the most capable APTs associated with Chinese state interests, showing advanced operational discipline, a modular toolkit of custom malware, and a strategic focus on telecommunications, defense logistics, and critical infrastructure.
Salt Typhoon’s hallmark is its technical precision. Rather than relying on social engineering or mass phishing, it infiltrates networks through supply-chain vulnerabilities and zero-day exploits. In recent operations documented by researchers, the group leveraged flaws in Citrix and Cisco systems to infiltrate European telecom providers, compromising backbone networks and data relays.
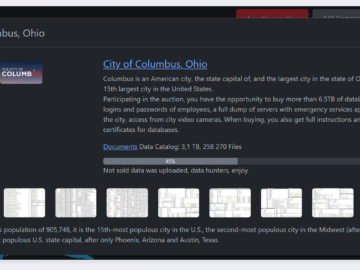
Salt Typhoon breached multiple organizations since early 2025, including Viasat, Canadian telecom firms, the U.S. Army National Guard, and Dutch government networks. Across all these incidents runs a consistent pattern: prolonged data exfiltration, silent observation, and compromise of infrastructure with the potential for command execution at scale.
If Salt Typhoon targeted Sistemi Informativi, the impact could be serious. As a key IT provider for Italian institutions, its systems could expose sensitive data and connections, allowing attackers to map critical parts of the country’s digital infrastructure.
The attack highlights a key weakness: reliance on third-party providers for national systems. Compromising one integrator can open access to many government databases, a tactic often linked to Salt Typhoon.
The Sistemi Informativi breach highlights that IT providers are now critical infrastructure and key targets. Cyber warfare has moved to networks, using exploits and AI-driven attacks. To stay resilient, Italy and Europe need not only stronger defenses but also better coordination between governments, industry, and intelligence.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Salt Typhoon)