A newly discovered Android spyware platform is raising concerns among cybersecurity researchers by introducing a business model that allows buyers to rebrand and resell surveillance malware as their own product.
Buyers can subscribe to the service, customize branding, and launch their own spyware operation with minimal effort.
KidsProtect presents itself as a parental monitoring app, a common tactic used in the stalkerware ecosystem.
By framing invasive surveillance features as child safety tools, developers attempt to appear legitimate while avoiding scrutiny from regulators and victims.
However, its promotion on hacking forums reveals a different intent. The spyware is advertised with phrases like “Built for Stability & Stealth” and includes features clearly designed for covert surveillance rather than parental oversight.
Researchers at Certo have identified a tool called “KidsProtect” that is being openly promoted online. Unlike traditional stalkerware, this platform is designed not just for use but for resale.
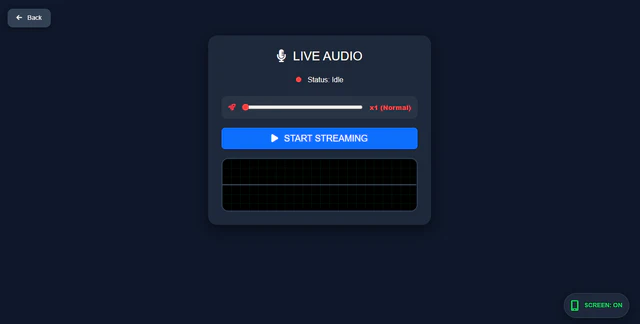
From a web-based dashboard, an operator can secretly record calls, stream live audio from the device’s microphone, track GPS location in real time, read SMS messages and notifications from apps including WhatsApp and Viber, log keystrokes.
The pricing model starts at around $60, with an additional white-label option that allows customers to create their own branded spyware business.
Extensive Surveillance Capabilities
Once installed on a device, KidsProtect operates silently in the background and provides attackers with near-total control via a web dashboard.
Key capabilities include:
- Real-time microphone streaming and call recording.
- GPS tracking with live location updates.
- Access to SMS messages and app notifications, including WhatsApp and Telegram.
- Keystroke logging to capture sensitive inputs like passwords.
- Remote access to front and rear cameras.
- Full access to contacts, photos, and stored data.
The malware also enables live screen monitoring, giving attackers visibility into everything happening on the device.

Technical analysis of the APK confirms that the spyware relies on extensive and sensitive Android permissions. These include access to location, microphone, camera, SMS, call logs, and external storage.
One of the most critical permissions abused is the Accessibility Service. Originally designed to assist users with disabilities, this feature allows apps to read screen content and interact with other applications.
In this case, it enables KidsProtect to capture messages, monitor app activity, and intercept credentials in real time.
KidsProtect incorporates multiple mechanisms to avoid detection and removal:
- The app disguises itself as “WiFi Service,” blending in with legitimate system components.
- It registers as a Device Administrator, preventing standard uninstallation.
- A built-in “anti-uninstall” feature ensures only the attacker can remove it.
- A BootReceiver component automatically restarts the spyware after reboot.
- Users are instructed to disable Google Play Protect before installation.
Additionally, the app requests permissions that allow it to run continuously in the background and avoid battery optimization restrictions.
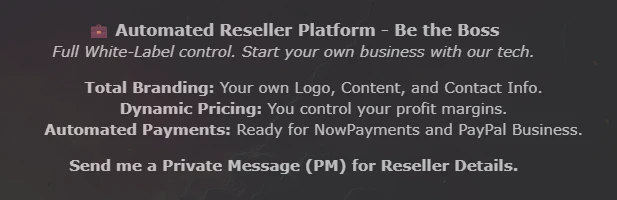
White-Label Model Expands Threat
The most concerning aspect of KidsProtect is its reseller model. Buyers can fully rebrand the spyware, set pricing, and distribute it under their own company name. This effectively turns surveillance malware into a franchise-style business.
This approach could undermine recent legal efforts to shut down stalkerware providers. Even as authorities take action against known companies, new operators can quickly emerge using the same underlying platform.
For example, several stalkerware services were taken offline in 2024 following court rulings, but white-label solutions like KidsProtect reduce the barriers to entry, allowing the ecosystem to regenerate rapidly.
The spyware operates under the package name “com.example.parentguard” and supports devices running Android 7 and above, with confirmed compatibility up to newer versions.
It allows cleartext traffic, increasing data exposure risks, and uses system-level permissions to maintain persistence.
Overall, KidsProtect highlights a shift in the stalkerware landscape from standalone tools to scalable, commercialized surveillance platforms that enable widespread abuse with minimal technical skill.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.