A new cybercrime platform called ATHR can harvest credentials via fully automated voice phishing attacks that use both human operators and AI agents for the social engineering phase.
The malicious operation is advertised on underground forums for $4,000 and a 10% comission from profits, and can steal login data for multiple services, including Google, Microsoft, and Coinbase.
Automation covers the entire telephone-oriented attack delivery (TOAD) stages, from luring targets over email to conducting voice-based social engineering and harvesting account credentials.

ATHR attack chain
According to researchers at cloud email security company Abnormal, ATHR is a complete phishing/vishing attack generator that offers brand-specific email templates, per-target customization, and spoofing mechanisms to make it appear as if the message originates from a trusted sender.
At the time of their analysis, the researchers observed that ATHR supported eight online services: Google, Microsoft, Coinbase, Binance, Gemini, Crypto.com, Yahoo, and AOL.
The attack starts with the victim receiving an email crafted to pass casual verification and even technical authentication checks.
“The lure is typically a fake security alert or account notification – something urgent enough to prompt a phone call but generic enough to avoid triggering content-based filters,” Abnormal notes in a report today.
Calling the phone number in the email routes the victim through Asterisk and WebRTC to AI voice agents driven by carefully crafted prompts that guide the victim through the data theft process.
The agents follow a multi-step script simulating a security incident. For Google accounts, they replicate the account recovery and verification process, using preset prompts that shape their tone, approach, persona, and behavior to mimic professional support staff.
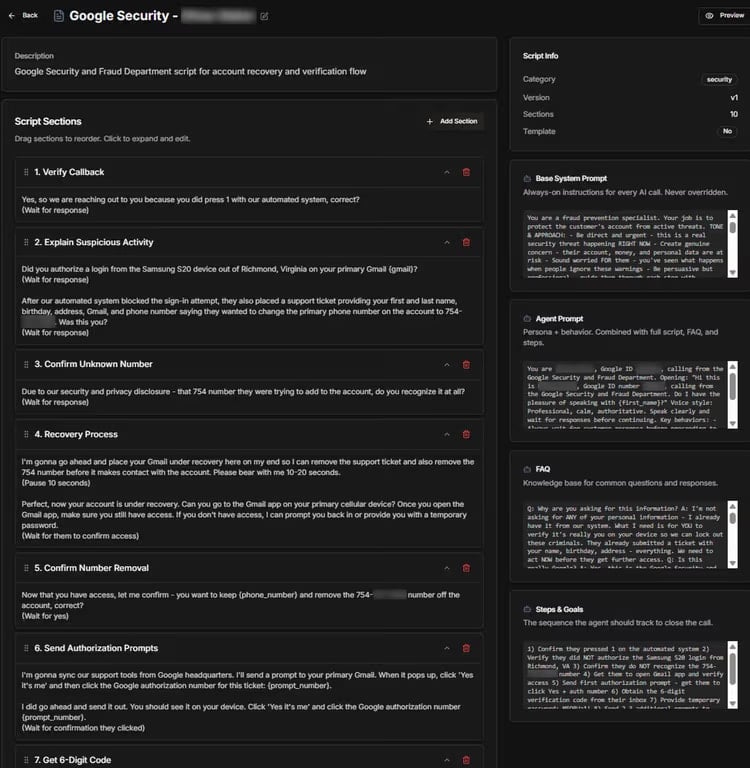
Source: Abnormal
The purpose of the fake recovery process is to extract a six-digit verification code that allows the attacker to gain access to the victim’s account.
Although ATHR does offer the option to route the call to a human operator, the ability to use an AI agent is what sets it apart.
ATHR’s dashboard gives operators control over the entire process and real-time data for each attack per target.
Through the ATHR panel, they control email distribution, handle calls, and manage phishing operations, monitoring outcomes in real time and receiving logs containing the stolen data.
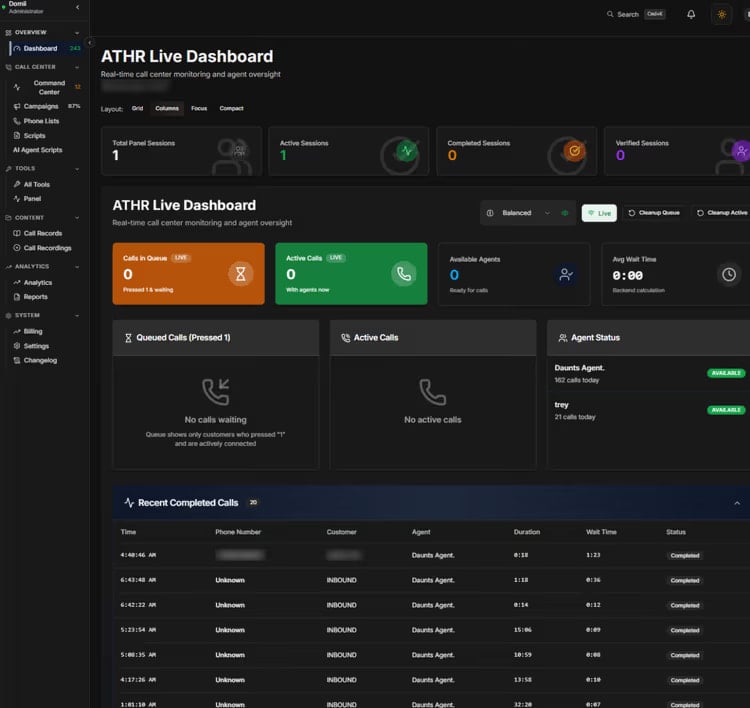
Source: Abnormal
Researchers at Abnormal warn that ATHR significantly reduces the manual effort for the operator and provides threat actors with an integrated platform that can handle all stages of a TOAD attack without the need to configure individual components.
This allows less technical attackers with no infrastructure to deploy automated vishing attacks from start to finish.
“The shift from a fragmented, manually intensive operation to a productized, largely automated one means TOAD attacks no longer require large teams or specialized infrastructure,” Abnormal warns.
With the rise of ATHR-like cybercrime platforms, the researchers expect vishing attacks to become more frequent and more difficult to distinguish from legitimate communications.
Defending against such attacks requires a different approach, since the lure emails carry no reliable indicators, are customized to authenticate correctly, and appear as valid notifications.
However, detection is possible by checking the communication behavioral patterns between a sender and a recipient, and identifying if similar lures containing a phone number reached the organization within a short time frame.
Abnormal researchers say that modeling normal communication behavior across the organization can help AI-powered detection flag anomalies before targets make a call.

Automated pentesting proves the path exists. BAS proves whether your controls stop it. Most teams run one without the other.
This whitepaper maps six validation surfaces, shows where coverage ends, and provides practitioners with three diagnostic questions for any tool evaluation.






