A new ransomware gang named ‘Money Message’ has appeared, targeting victims worldwide and demanding million-dollar ransoms not to leak data and release a decryptor.
The new ransomware was first reported by a victim on the BleepingComputer forums on March 28, 2023, with Zscaler’s ThreatLabz soon after sharing information on Twitter.
Currently, the threat actor lists two victims on its extortion site, one of which is an Asian airline with annual revenue close to $1 billion. Additionally, the threat actors claim to have stolen files from the company and include a screenshot of the accessed file system as proof of the breach.
.jpg)
While investigating, BleepingComputer has seen evidence of a potential Money Message breach on a well-known computer hardware vendor. However, we have not been able to independently confirm the attack with the company at this time.
How Money Message encrypts a computer
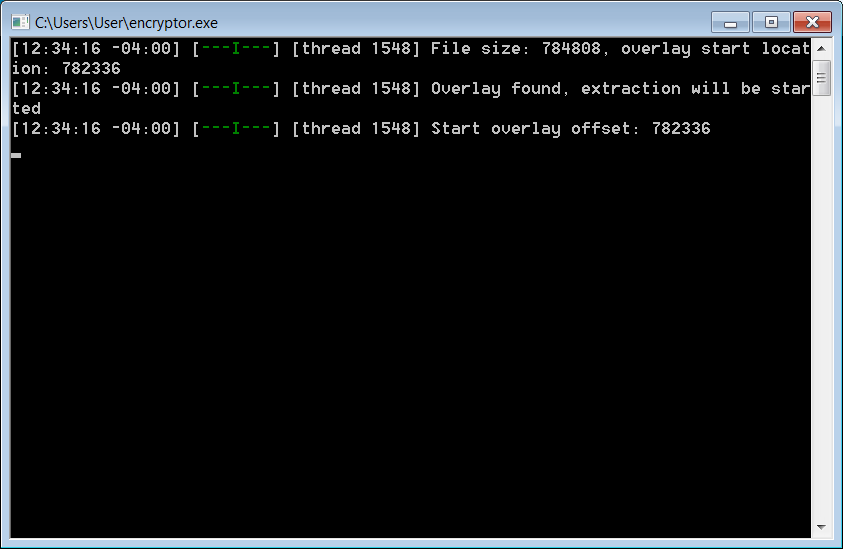
The Money Message encryptor is written in C++ and includes an embedded JSON configuration file determining how a device will be encrypted.
This configuration file includes what folders to block from encrypting, what extension to append, what services and processes to terminate, whether logging is enabled, and domain login names and passwords likely used to encrypt other devices.
In the sample analyzed by BleepingComputer, the ransomware will not encrypt files in the following folders:
C:msocache,C:$windows.~ws,C:system volume information,C:perflogs,C:programdata,C:program files (x86), C:program files,C:$windows.~bt,C:windows,C:windows.old,C:boot]When launched, it will delete Shadow Volume Copies using the following command:
cmd.com /c vssadmin.exe delete shadows /all /quiet to clear shadow volume copiesThe ransomware will then terminate the following process:
sql.exe,oracle.exe,ocssd.exe,dbsnmp.exe,synctime.exe,agntsvc.exe,isqlplussvc.exe,xfssvccon.exe,mydesktopservice.exe,ocautoupds.exe,encsvc.exe,firefox.exe,tbirdconfig.exe,mdesktopqos.exe,ocomm.exe,dbeng50.exe,sqbcoreservice.exe,excel.exe,infopath.exe,msaccess.exe,mspub.exe,onenote.exe,outlook.exe,powerpnt.exe,steam.exe,thebat.exe,thunderbird.exe,visio.exe,winword.exe,wordpad.exe,vmms.exe,vmwp.exeNext, the ransomware shuts down the following Windows services:
vss, sql, svc$, memtas, mepocs, sophos, veeam, backup, vmmsWhen encrypting files, it will not append any extension, but this can change depending on the victim. According to security researcher rivitna, the encryptor uses ChaCha20/ECDH encryption when encrypting files.
The only files excluded from encryption by default are:
- desktop.ini
- ntuser.dat
- thumbs.db
- iconcache.db
- ntuser.ini
- ntldr
- bootfont.bin
- ntuser.dat.log
- bootsect.bak
- boot.ini
- autorun.inf
During our tests, the encryption of the files by Money Message was fairly slow compared to other encryptors.
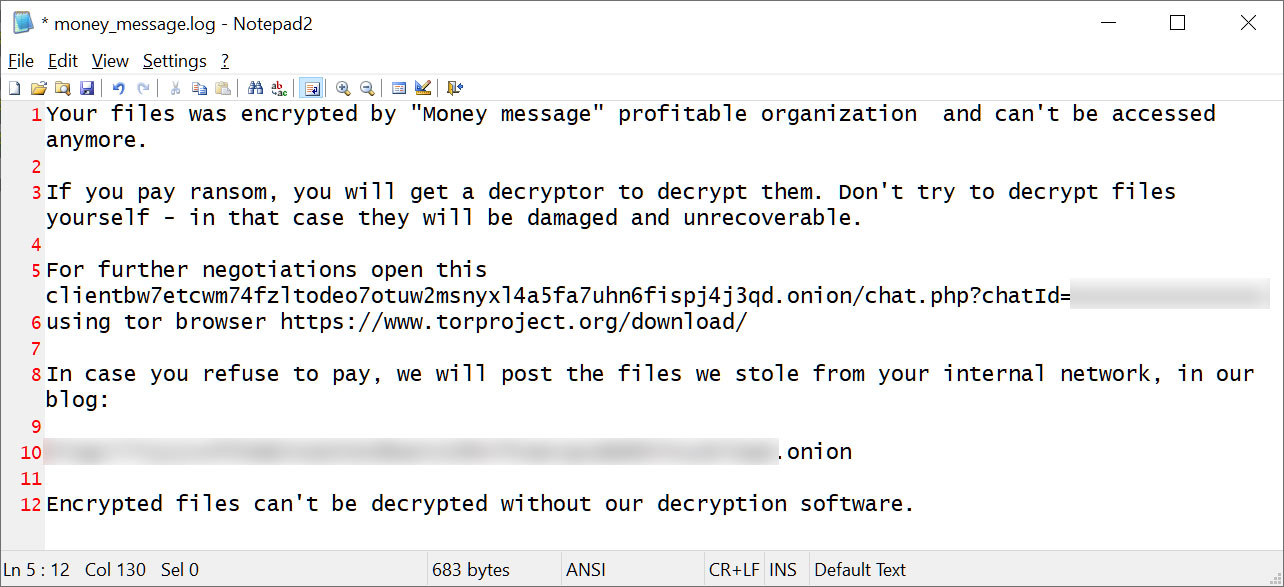
After encrypting the device, the ransomware will create a ransom note named money_message.log that contains a link to a TOR negotiation site used to negotiate with the threat actors.
The ransomware will also warn that they will publish any stolen data on their data leak site if a ransom is not paid.
The emergence of the Money Message ransomware group introduces an additional threat that organizations need to watch out for.
Although the encryptor used by the group does not appear sophisticated, it has been confirmed that the operation is successfully stealing data and encrypting devices during their attacks.
Experts will analyze the ransomware, and if a weakness in the encryption is found, we will update this post.






