PLAYFULGHOST, a Gh0st RAT variant, leverages distinct traffic patterns and encryption, which spread via phishing emails and SEO poisoning of bundled applications, enabling keylogging, screen capture, and other malicious remote access capabilities.
A phishing campaign employed a .jpg file as a lure to deliver a malicious RAR archive. Upon extraction and execution, the archive released a Windows executable, which subsequently downloaded and executed the malware known as PLAYFULGHOST from a remote server.

The SEO poisoning campaign involves a malicious installer disguised as legitimate software, which, upon execution, downloads and installs additional malicious components, including PLAYFULGHOST, from a remote server.


The malicious process downloads PLAYFULGHOST components, as a vulnerable executable loads a malicious DLL, which decrypts and loads the PLAYFULGHOST payload into memory, exploiting DLL search order hijacking.
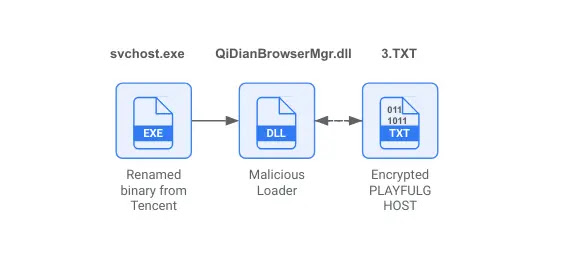
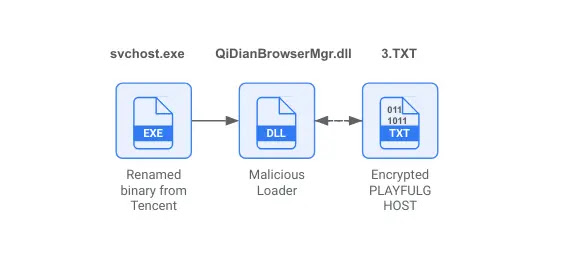
Researchers observed two PLAYFULGHOST malware execution scenarios, as in scenario 1, a renamed Tencent svchost.exe loaded a malicious DLL named QiDianBrowserMgr.dll, which delivered a 3.TXT payload, while in scenario 2, a renamed curl.exe (TIM.exe) loaded libcurl.dll to deliver a Debug.log payload.
PLAYFULGHOST alongside BOOSTWAVE, a shellcode dropper, TERMINATOR, a tool to terminate security software, QAssist.sys, a rootkit to hide malicious activity, and CHROMEUSERINFO.dll was found, indicating an intent to steal Google Chrome credentials.
According to Mandiat researchers, with the help of these tools, the adversary is able to demonstrate their focus on evading detection, maintaining persistence, and data exfiltration.


It persists on the system by leveraging a combination of mechanisms, including registry key entries, scheduled tasks, the startup folder, and also may utilize a Windows Service for robust background operations.
PLAYFULGHOST is a sophisticated malware capable of remote system control, including data exfiltration (keylogging, screenshots, audio), file manipulation, remote execution (shell, RDP), privilege escalation, and anti-forensic techniques.
Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free