The intel teams here at Red Canary and Zscaler have seen some notable social engineering attacks recently. Bad actors get an employee email address and run a program to plug it into a bunch of legitimate sites that send mail—newsletter signups and the like. They get bombarded with emails. Then the adversary reaches out, either by phone or email, pretending to be IT and offering to help fix their spam problem. It’s something we’ve seen in the past—an elaborate hoax and one that’s easier to fall for because of the fatigue of endless email spam.
Attacks like these are complicated to defend against. Using social engineering, bad actors can get ahold of valid credentials. They appear to be just another user, making them particularly hard to detect. They also attack broadly, trying the same tactics against many employees.
Red Canary and Zscaler together have a distinct advantage against these, and many other types of attacks. And now with our latest release, that advantage has grown.
Trigger ZIA response actions in Red Canary
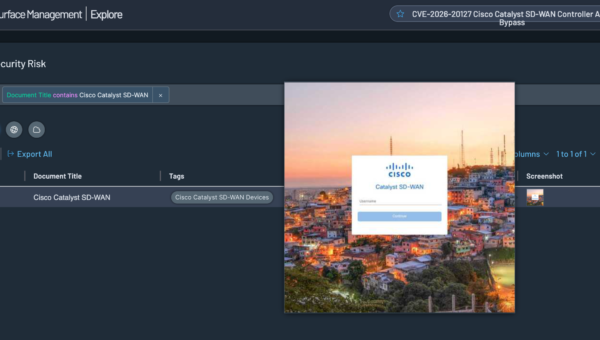
The new integration gives teams an easy way to update Zscaler Internet Access (ZIA) network policies using Red Canary response actions, so they can instantly enforce a network-wide perimeter around a threat, regardless of where the user is or what device they are using. It’s a straightforward way to turn “we confirmed this URL/domain/IP is malicious” into “it’s blocked for everyone,” without extra back-and-forth between tools.
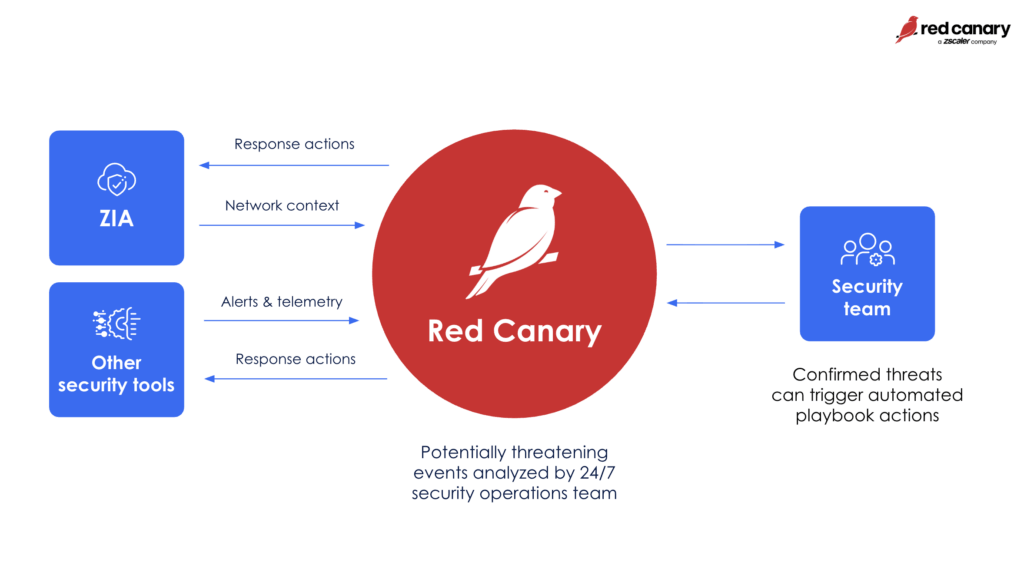
Users can choose from a set of pre-built, expert-checked actions (like blocking a URL/domain/IP or removing a risky allowlist entry), and they can set these actions to trigger automatically or only after manual approval. Every action is tracked in both Red Canary and Zscaler, so teams can see what happened and why.
Key capabilities
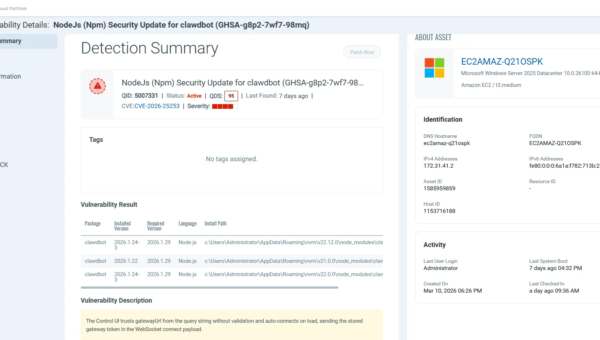
- Automated IOC blocking: Instantly add malicious IP addresses or domains to Destination IP Groups and apply ZIA policies to restrict access.
- Unmanaged device isolation: Add internal IP addresses for compromised devices to Source IP Groups and apply ZIA policies to restrict network access.
- Granular URL filtering: Add malicious URLs to custom URL Categories and apply ZIA policies to restrict access or enforce browser isolation.
- Malicious file protection: Add malicious file hashes to the ZIA Sandbox Denylist and ensure that Zscaler quickly identifies and quarantines future instances of the file encountered in the wild.
- Bi-directional automation: Every “add” action also has a supported “remove” action–easily revert actions once an investigation is closed and the threat is mitigated.
Why it matters
Remember that spam bombing campaign we started with? If that’s successful, the attacker gets their hands on valid credentials, meaning that the next steps can look almost indistinguishable from everyday work. It can look like a real user signing in, using trusted apps, and leaning on existing tools to stay under the radar. Luckily, Red Canary analytics are built to catch the quiet signals—logins and sequences of activity that don’t fit the user, and living-off-the-land behavior that hides in plain sight.
Combine that with new, in-workflow response actions, and detection turns into protection even faster. As soon as Red Canary verifies the threat, teams can push the right ZIA action—like blocking the malicious destination—without switching consoles or waiting on manual follow-up. You can also automate these actions with playbooks. The result is a tighter loop from “we see it” to “we stop it,” helping you contain an attack quickly and reduce the chance it spreads to more users. Crucially, because ZIA acts as the gateway, this protection extends to every device on your network, including unmanaged hardware and IoT where an endpoint agent cannot be installed.
That means:
- Drastic reduction in MTTR—move from detection to network-wide block in seconds, not hours of manual ticket routing between security and networking teams
- Broader, network-level protection, so no one hits a phishing page even if they click the link
- Agentless enforcement at the edge instantly shields your entire environment, including unmanaged and IoT devices, where traditional EDR agents can’t go
- Less manual work with fewer console pivots
Interested in how ZIA response actions in Red Canary can protect your organization?
Get a demo!