Security researchers at watchTowr Labs have disclosed a critical exploit chain in the Progress ShareFile Storage Zone Controller.
The vulnerabilities, tracked as CVE-2026-2699 and CVE-2026-2701, enable unauthenticated attackers to achieve Remote Code Execution (RCE) and completely compromise vulnerable servers.
With roughly 30,000 instances exposed to the public internet, organizations are urged to patch immediately to prevent catastrophic data breaches.
Managed file transfer (MFT) solutions remain a top target for advanced persistent threat (APT) groups and ransomware syndicates.
Following historic breaches involving tools like MOVEit, Cleo Harmony, and GoAnywhere, threat actors continuously hunt for unpatched data-sharing gateways.
These newly uncovered ShareFile flaws present a highly lucrative opportunity for attackers looking to infiltrate corporate networks and siphon sensitive intellectual property.
The Target: Storage Zone Controller
While Progress ShareFile operates a popular SaaS platform, many enterprises utilize the on-premises Storage Zone Controller to maintain data sovereignty and regulatory compliance.
This software acts as a customer-managed gateway, allowing organizations to keep files on local network shares or private cloud buckets while still utilizing the main ShareFile web interface.
The newly discovered vulnerabilities reside entirely within this self-hosted application.
CVE-2026-2699: Bypassing Authentication
The attack sequence begins with an authentication bypass in the administrator configuration panel (/ConfigService/Admin.aspx).
When an unauthenticated user requests this endpoint, the application issues an HTTP 302 redirect, pointing the user to a secure login page.
However, researchers discovered a fatal coding error in the underlying C# codebase. The developers passed a false boolean flag to the .Redirect() function.
This specific flag instructs the server not to terminate the page’s execution after sending the redirect command.
Known as an “Execution After Redirect” (EAR) vulnerability, this allows an attacker to simply intercept the HTTP response, drop the Location header, and load the fully functional admin panel, no credentials required.
CVE-2026-2701: Achieving Remote Code Execution
With administrative access secured, the attacker can exploit the second vulnerability to execute malicious code.
The Storage Zone Controller allows administrators to configure a “Network Share Location” for user uploads.
While the application tests the provided path to ensure it has read and write permissions, it completely fails to validate whether the path is a legitimate, safe storage directory.
Attackers can exploit this oversight by reconfiguring the storage destination to point directly into the application’s public webroot (C:inetpubwwwrootShareFileStorageCenterdocumentum).
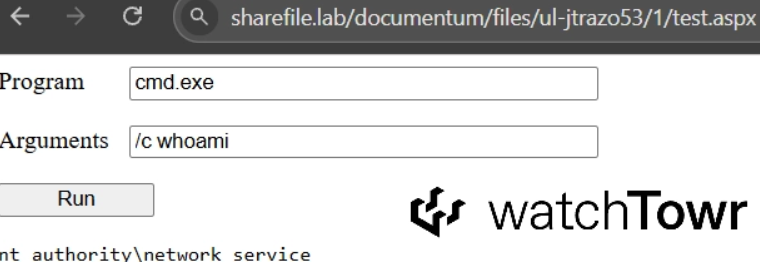
Once the path is modified, the attacker can upload a malicious ASPX web shell disguised as a standard file.
By navigating to that uploaded script in their browser, the attacker gains full, unauthorized remote control over the server.
These vulnerabilities specifically impact Branch 5.x of the ShareFile Storage Zone Controller, which is built on ASP.NET.
The flaws were confirmed by WatchTowr Labs in version 5.12.3. Progress addressed both vulnerabilities in version 5.12.4, which was quietly rolled out to customers on March 10, 2026.
Security teams must immediately upgrade their Storage Zone Controllers to version 5.12.4 or later.
Additionally, defenders should monitor web server logs for anomalous requests to configuration endpoints, inspect the webroot for unexpected ASPX files, and ensure that on-premises file gateways are shielded behind robust firewalls wherever possible.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.