The maintainers of the Python Package Index (PyPI) repository briefly suspended new user sign-ups following an influx of malicious projects uploaded as part of a typosquatting campaign.
It said “new project creation and new user registration” was temporarily halted to mitigate what it said was a “malware upload campaign.” The incident was resolved 10 hours later, on March 28, 2024, at 12:56 p.m. UTC.
Software supply chain security firm Checkmarx said the unidentified threat actors behind flooding the repository targeted developers with typosquatted versions of popular packages.
“This is a multi-stage attack and the malicious payload aimed to steal crypto wallets, sensitive data from browsers (cookies, extensions data, etc.), and various credentials,” researchers Yehuda Gelb, Jossef Harush Kadouri, and Tzachi Zornstain said. “In addition, the malicious payload employed a persistence mechanism to survive reboots.”
The findings were also corroborated independently by Mend.io, which noted that it detected more than 100 malicious packages targeting machine learning (ML) libraries such as Pytorch, Matplotlib, and Selenium.

The development comes as open-source repositories are increasingly becoming an attack vector for threat actors to infiltrate enterprise environments.
Typosquatting is a well-documented attack technique in which adversaries upload packages with names closely resembling their legitimate counterparts (e.g., Matplotlib vs. Matplotlig or tensorflow vs. tensourflow) in order to trick unsuspecting users into downloading them.
These deceptive variants – totalling over 500 packages, per Check Point – have been found to be uploaded from a unique account starting March 26, 2024, suggesting that the whole process was automated.
“The decentralized nature of the uploads, with each package attributed to a different user, complicates efforts to cross-identify these malicious entries,” the Israeli cybersecurity company said.
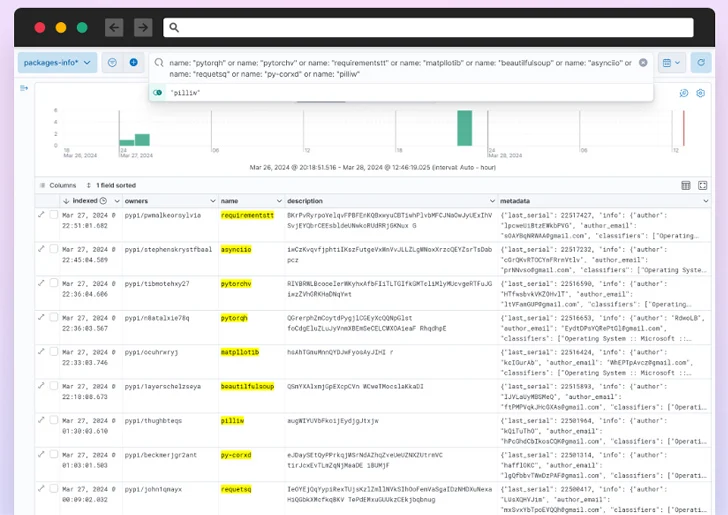
Cybersecurity firm Phylum, which has also been tracking the same campaign, said the attackers published –
- 67 variations of requirements
- 38 variations of Matplotlib
- 36 variations of requests
- 35 variations of colorama
- 29 variations of tensorflow
- 28 variations of selenium
- 26 variations of BeautifulSoup
- 26 variations of PyTorch
- 20 variations of pillow
- 15 variations of asyncio
The packages, for their part, check if the installer’s operating system was Windows, and if so, proceed to download and execute an obfuscated payload retrieved from an actor-controlled domain (“funcaptcha[.]ru”).

The malware functions as a stealer, exfiltrating files, Discord tokens, as well as data from web browsers and cryptocurrency wallets to the same server. It further attempts to download a Python script (“hvnc.py”) to the Windows Startup folder for persistence.
The development once again illustrates the escalating risk posed by software supply chain attacks, making it crucial that developers scrutinize every third-party component to ensure that it safeguards against potential threats.
This is not the first time PyPI has resorted to such a measure. In May 2023, it temporarily disabled user sign-ups after finding that the “volume of malicious users and malicious projects being created on the index in the past week has outpaced our ability to respond to it in a timely fashion.”
PyPI suspended new user registrations a second-time last year on December 27 for similar reasons. It was subsequently lifted on January 2, 2024.