When ransomware hits, decisions move fast. Ransomware negotiations begin at one of the most stressful moments in an incident: once a victim has been compromised and the decision has been made to open a channel with cybercriminals. Victims usually seek to reduce the ransom demanded, secure a decryption key or prevent the release of stolen data. Authorities discourage paying ransoms because it finances criminal activity, offers no guarantee of full data recovery and encourages further attacks — against the victim and others. Despite these warnings, many organizations still choose to negotiate with threat actors who will test boundaries, exploit uncertainty, and adjust pressure based on what they learn. This often happens when critical business operations are severely threatened, particularly in sectors such as health care where patient lives may be at stake or when manufacturing systems are down.
Our new report, Ransomware Negotiations: An Overview of Process and Tactics Used, evaluates modern ransomware negotiation practices and the evolving tactics of increasingly professionalized threat groups that treat the extortion process as a revenue-optimized “sales” cycle. Dedicated negotiation teams, sophisticated pressure tactics, tiered pricing models based on victim size, intelligence gathering and data analysis are used to fuel extortion outcomes and higher profits. This blogpost provides an overview of the full report, which is available for download here.
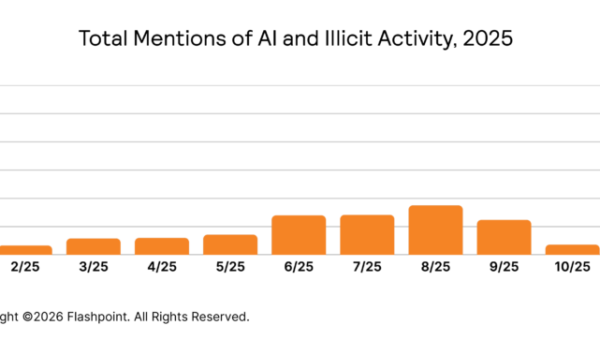
The negotiation lifecycle
The ransomware negotiation process spans the victim’s initial decision to make contact with the threat actor through the sustained period of back-and-forth negotiation and finally culminating in one of two major resolutions: a successful payment and the provision of a decryption key to the victim or the threat actor’s decision to publicly expose the victim’s proprietary or sensitive data on a dedicated data leak site (DLS). This comprehensive process involves technical recovery considerations as well as significant psychological, financial and legal calculations for the affected organization.
Figure 1: The image depicts stages of the ransomware negotiation process.
Ransomware negotiations typically last several days to a week or two depending on factors such as the ransomware group, victim complexity, ransom amount, negotiation strategy and whether the victim pays or stalls for time — to investigate backups or involve law enforcement, for example. Attackers often set deadlines to create urgency, but these are frequently extended during back-and-forth discussions. A typical negotiation timeline may be represented as follows:

Figure 2: The image depicts a typical ransomware negotiation timeline.
Proof of claim: a few decrypted files for free
One of the most common features of modern ransomware negotiations is the “proof” step. Particularly in double-extortion cases (encryption plus data theft), threat actors often allow victims to decrypt two or three small, low-importance files for free. This trial decryption helps the attacker establish credibility, momentum and control.
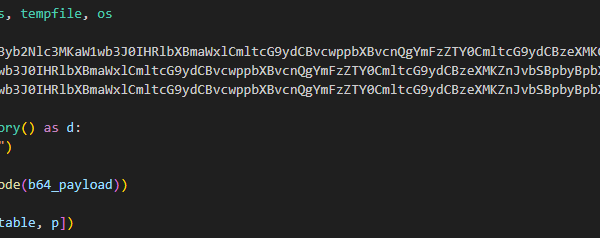
The victim typically receives a ransom note that instructs them to contact the attackers via email, Telegram, Tor-based sites, Tox chat or a victim negotiation portal and explicitly mentions attaching encrypted test files. Some groups upload unencrypted samples of exfiltrated data on their DLSs, but encrypted samples are often processed privately in chats to prove decryption capabilities. Ransomware groups such as Akira, LeakNet, LockBit and Nova include a specific offer in their ransom notes: they will decrypt several test files — usually two or three — as proof of their ability to restore the compromised data and emphasize not to use third-party recovery tools as they may corrupt files permanently.
CISOs should treat proof-of-decryption as a validation checkpoint, not a reassurance. A successful test does not guarantee fast, complete or safe decryption at scale. Proof reduces uncertainty, but it doesn’t remove risk.
Ransom prices are not random
Ransomware groups approach extortion as a business operation focused on revenue generation. They determine ransom demands through a calculated, business-like methodology designed to maximize profit while keeping the value “realistic” enough to incentivize the victim to pay. These demands frequently are adjusted based on information gathered during reconnaissance and post-compromise assessment activities. One of the biggest variables is the victim’s perceived financial capacity. Groups research revenue, annual reports, market cap (in cases where the victim is a public company), employee count, industry profitability and, sometimes, cyber insurance details.
For example, the Akira and Black Field ransomware groups demonstrate their approach to setting ransom demands in ransom notes, stating, “We will study in depth your finance, bank & income statements, your savings, investments etc. and present our reasonable demand to you.”
Across observed incidents, ransomware operators commonly ask for amounts roughly in the 1% to 5% range of a victim’s revenue, with smaller organizations sometimes facing higher proportional demands because attackers assume operational fragility increases payment likelihood.
Download the report
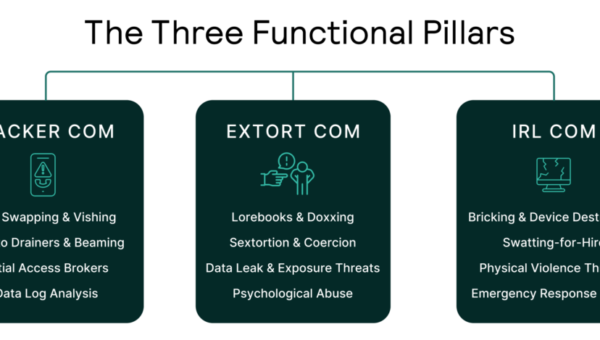
Download Ransomware Negotiations: An Overview of Process and Tactics Used to discover our full analysis of how the highest impact ransomware-as-a-service (RaaS) operations negotiate with and apply pressure to victims. The analysis covers observed negotiation tactics used by groups including Qilin, Akira, Kill Security, LockBit, RansomHub,, and their adoption of a variety of methods to enhance extortion outcomes, including victim data auditing, the establishment of intelligence gathering units, language assistance service, hacker tutorials and professional narrative development for phishing. The report also looks at new ransomware payment reporting regulations, the emergence of data auditing service providers to the ransomware ecosystem, notable multi-extortion techniques and the use of cyber insurance as a pricing signal.
What this means for CISOs
For CISOs, the most important lesson is to treat negotiation as a structured adversarial process. Threat actors will test boundaries, exploit uncertainty, and adjust pressure based on what they learn. Meanwhile, new reporting obligations and anti-extortion policy trends are increasing the legal complexity of payment decisions, potentially reducing payment rates and pushing threat actors toward even more coercive tactics. Negotiations could become both more professionalized and more aggressive as victims and governments make it harder for criminals to get paid.