A critical remote code execution (RCE) flaw in Ivanti Endpoint Manager Mobile (EPMM), tracked as CVE-2026-1281, is being heavily exploited. GreyNoise shows that 83% of observed attacks come from a single IP address: 193[.]24[.]123[.]42.
This IP is registered to PROSPERO OOO (AS200593) and labeled as “bulletproof” hosting by Censys. Surprisingly, this IP was missing from many early indicators of compromise (IOCs) shared with defenders.

Two Critical Vulnerabilities Under Active Attack
CVE-2026-1281 (CVSS 9.8) allows unauthenticated attackers to execute system commands by abusing Bash arithmetic expansion in backend file-delivery scripts.
A second flaw, CVE-2026-1340 (also CVSS 9.8), enables similar code execution in another EPMM component.
On January 29, Ivanti released its advisory. Soon after, the Cybersecurity and Infrastructure Security Agency (CISA) added CVE-2026-1281 to its Known Exploited Vulnerabilities catalog.
Dutch authorities later confirmed breaches at the Dutch Data Protection Authority (AP) and the Council for the Judiciary (RVDR), indicating that attacks were already underway before many organizations had patched.
Between February 1 and 9, GreyNoise recorded 417 exploitation sessions from eight IPs. On February 8 alone, 269 sessions were observed, about 13 times the earlier daily average.

The main IP, 193[.]24[.]123[.]42, is also linked to attacks on Oracle WebLogic Server, GNU Inetutils telnetd, and GLPI. The attacker rotates hundreds of user-agent strings, suggesting automated mass exploitation.
IOC Gaps and Infrastructure Risks
Some widely shared IOCs did not match Ivanti exploitation data. For example, Windscribe VPN exit nodes on M247 infrastructure generated heavy traffic, but none targeted Ivanti EPMM.
Another IOC pointed to a residential router used only for limited activity. Organizations that blocked only those VPN or residential IPs, but not AS200593, may have missed the main threat source.

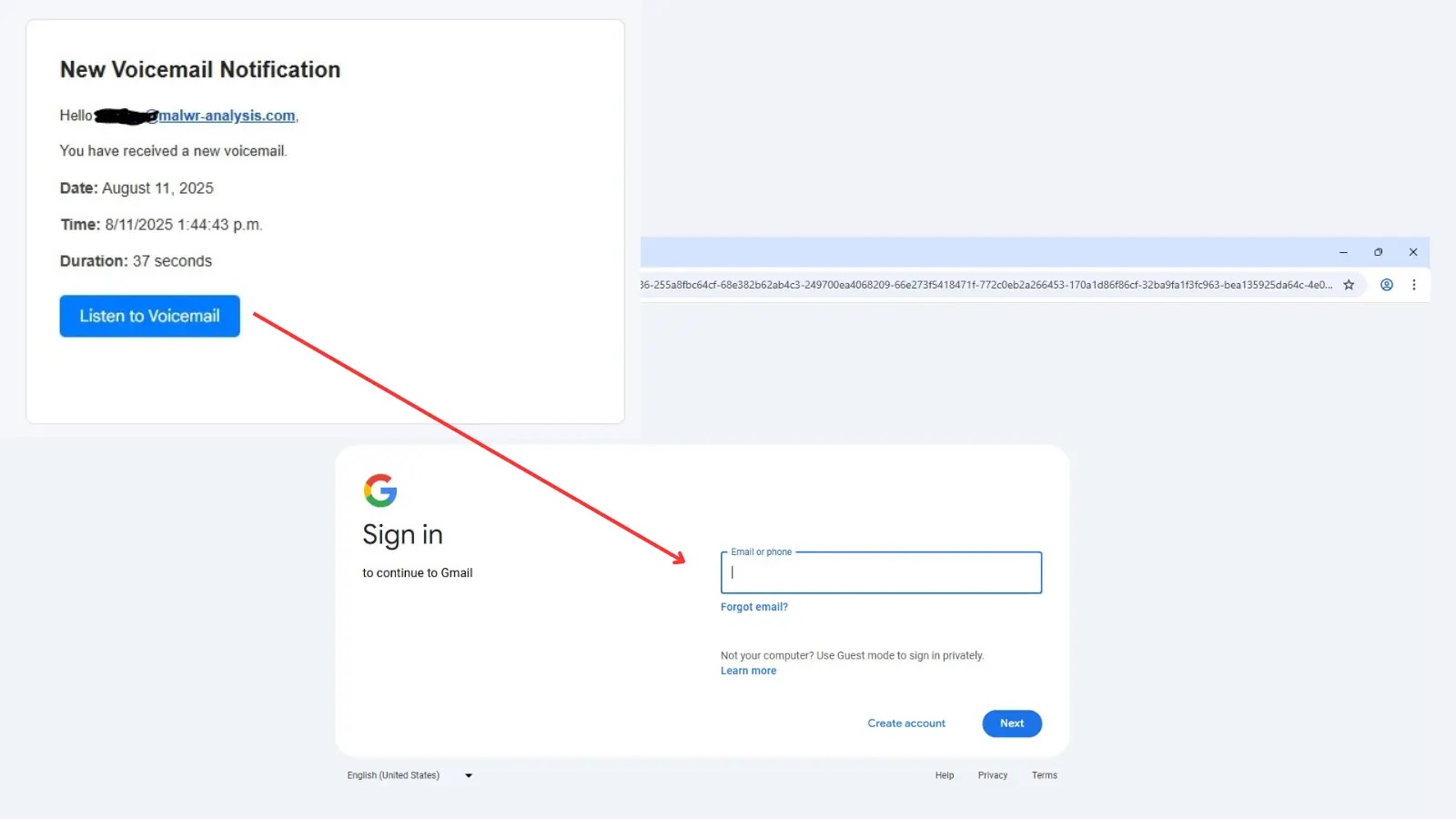
About 85% of payloads used DNS callbacks to confirm code execution instead of immediately dropping malware. This behavior matches initial access broker tactics.
Reports also describe “sleeper” webshells at /mifs/403.jsp that stay dormant until triggered. This means even patched systems could remain compromised if attackers gained access before remediation.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.