A sophisticated phishing campaign targets wedding planners and vendors with stealer malware disguised as Microsoft Teams meetings. Security researchers highlight the use of compromised legitimate emails to build trust before delivering payloads.
Threat actors impersonate legal professionals in emails from czimmerman@craigzlaw[.]com, a domain tied to The Law Offices of Craig Zimmerman, a real consumer protection firm. Messages include realistic details like wedding dates, guest counts, and venues to mimic vendor coordination.
After email exchanges, victims receive a fraudulent Teams link: https://teams.microsoft.com/l/meet/47018czL7LJ5PZQ6Cy, prompting a video call for “optimal video quality.”
This tactic exploits high trust in collaboration tools amid wedding industry pressures. that such attacks appear highly convincing and evade casual scrutiny. Similar Teams abuses have surged, with hackers using chats for malware since 2022.
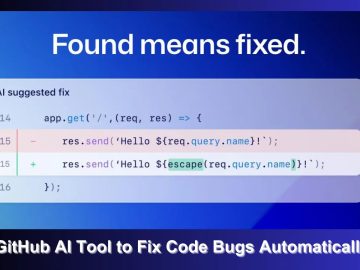
Clicking the link redirects to ussh[.]life/connect/teamsfinal/9/windows, a malicious site masquerading as a Teams download page. It urges downloading executables labeled for Windows, including a system reference prompt. Analysis reveals stealer malware behavior: executables likely harvest credentials, browser data, and session tokens post-infection.
The site employs social engineering, mimicking official Microsoft branding with prompts like “Need help? System reference.” Downloads evade basic AV via obfuscation, common in info-stealers like those in DarkGate campaigns via Teams. Once executed, stealers exfiltrate data to attacker C2, enabling account takeovers for further phishing.
Wedding-themed lures parallel Android stealers like Tria, which use invites to steal SMS and email, but this Windows variant targets planners on desktops.
Indicators of Compromise
- Email: czimmerman@craigzlaw[.]com (compromised legitimate domain)
- Phishing URL: https://teams.microsoft.com/l/meet/47018czL7LJ5PZQ6Cy
- Malware host: ussh[.]life/connect/teamsfinal/9/windows
- Fake code: fr6c (embedded in redirect)
Block these IOCs at firewalls; scan with EDR for anomalous Teams traffic.
Targets include U.S. wedding vendors, leveraging seasonal rushes. Compromised lawyer emails suggest initial breach via phishing or credential stuffing on M365 accounts. Victims risk data breaches exposing client PII, payments, and contracts.
Verify sender domains; hover over Teams links before clicking. Enable Microsoft 365 ATP for external access restrictions. Train staff on vishing via fake calls. Use passwordless auth and monitor for unusual downloads from collaboration tools. Wedding firms should segment vendor comms to email-only.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.