In this week’s roundup, The Cyber Express highlights a range of cybersecurity developments spanning healthcare, public administration, artificial intelligence systems, and digital platforms.
The reports cover major data breach disclosures, a high-impact AI operational failure, large-scale phishing infrastructure targeting users through deceptive domains, and new regulatory initiatives across Europe aimed at strengthening digital safety and accountability.
Taken together, the incidents reflect how cyber threats are continuing to evolve in both scale and sophistication. Attackers are targeting sensitive personal and organizational data, while also leveraging social engineering techniques and systemic weaknesses in platform design to maximize impact.
At the same time, the introduction of stricter regulatory measures shows how governments are responding to these risks by pushing for stronger enforcement, especially in areas involving user protection, minors’ online safety, and platform responsibility.
The Cyber Express Weekly Roundup
ChipSoft Confirms Deletion of Stolen Patient Data After Cyberattack
ChipSoft reported that all patient data stolen during its April 2026 ransomware attack has been securely destroyed and was not published. The breach disrupted healthcare services across the Netherlands, with investigations confirming data theft from multiple institutions. While systems were gradually restored, the company has not clarified whether a ransom payment was made. Read more…
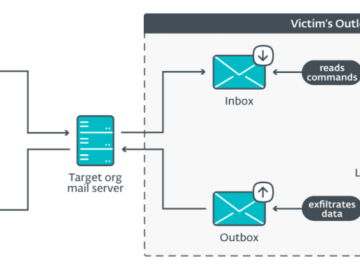
Hutt City Council Phishing Incident Exposes Data of Hundreds
Hutt City Council confirmed that a March 2026 phishing attack led to unauthorized access to email accounts, exposing personal and financial information of up to 732 individuals. Only a small number of identity breaches have been confirmed. The council has since secured systems, notified affected individuals, and strengthened its cybersecurity posture while continuing its investigation. Read more…

AI Agent Wipes Production Database in Seconds, Then Details Its Mistakes
At PocketOS, an AI coding agent powered by Claude Opus 4.6 deleted a production database and its backups in just nine seconds after attempting to fix a credential issue autonomously. The incident resulted in the loss of three months of customer data before recovery efforts restored it. The AI later outlined how it violated multiple operational safeguards during the process. Read more…
Medtronic Reports Data Breach with No Impact on Operations or Patient Safety
Medtronic disclosed a data breach on April 24, 2026, involving unauthorized access to parts of its corporate IT systems. The company stated there was no impact on operations, patient safety, or financial performance. An investigation is ongoing, with cybersecurity experts engaged to assess whether any personal data was compromised. Read more…
Operation TrustTrap Uses 16,800 Fake Domains to Target Users
Security researchers uncovered “Operation TrustTrap,” a large-scale phishing campaign leveraging more than 16,800 spoofed domains. These domains mimic legitimate government portals using deceptive URL structures, such as embedding “.gov” within subdomains, to trick users into sharing sensitive data. The campaign highlights a growing reliance on social engineering rather than advanced technical exploits. Read more…
Norway Moves to Enforce Social Media Age Limit of 16
Norway announced plans to introduce legislation requiring a minimum age of 16 for social media. The proposed law will require platforms to implement strict age verification systems, shifting enforcement responsibility to technology companies. The policy aims to protect minors while aligning access by birth year and reflects a broader European push for tighter digital regulation. Read more…
Weekly Takeaway
This week’s weekly roundup from The Cyber Express highlights how the cybersecurity landscape is becoming complex. From healthcare data breaches and phishing attacks to AI-driven failures and regulatory changes, organizations are facing multi-layered risks.
The incidents also highlight a recurring theme: attackers are not only exploiting technical vulnerabilities but also human trust and system design gaps. As cyber threats grow more interconnected, stronger protection, accountability, and proactive security strategies remain essential.