The race most security programs are built around — patch faster than the attacker can exploit — was designed for a threat landscape that no longer exists. The data shows defenders are falling behind in the vast majority of cases. Across the most critical, actively weaponized vulnerabilities of the past four years, manual remediation processes failed to keep pace with attackers 88% of the time. Half were weaponized before a patch even existed. But the data also proves the inverse: 15% of organizations that operationalized their remediation pipeline patched by the point of KEV addition — proof that the gap is closable when the model changes.
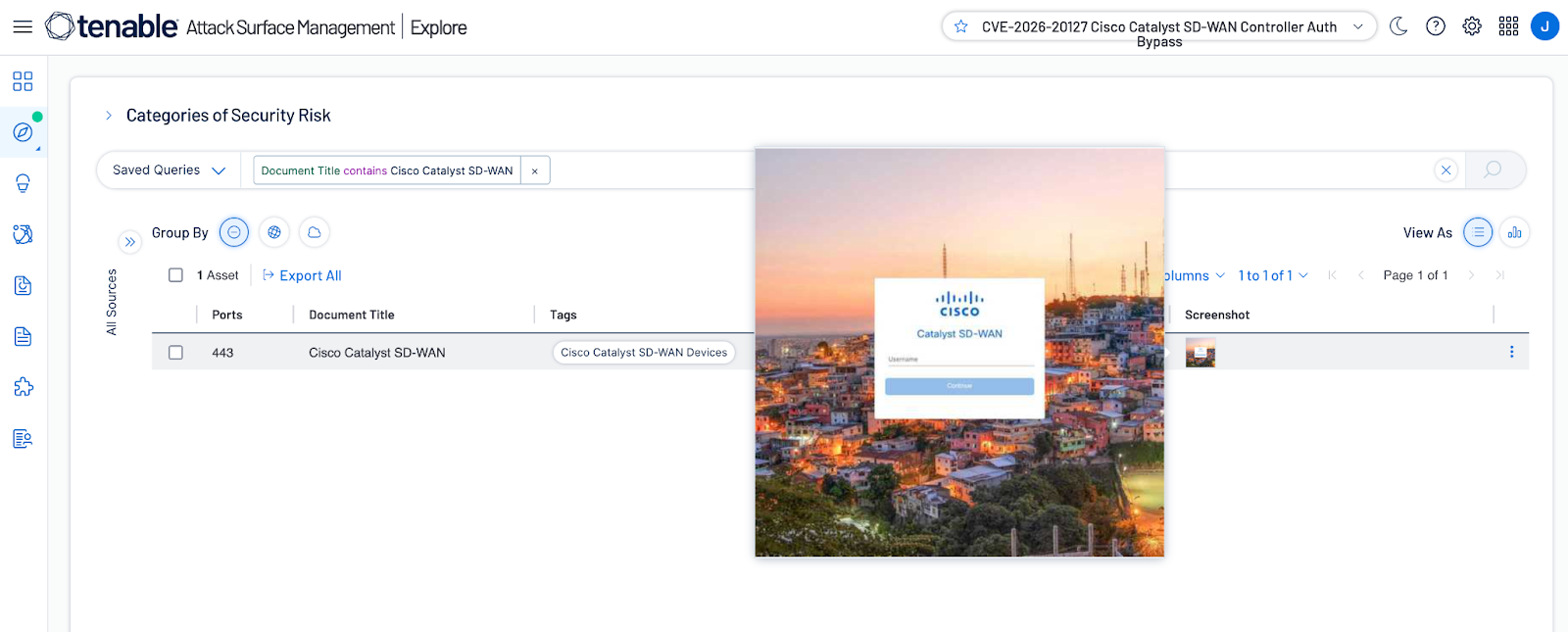
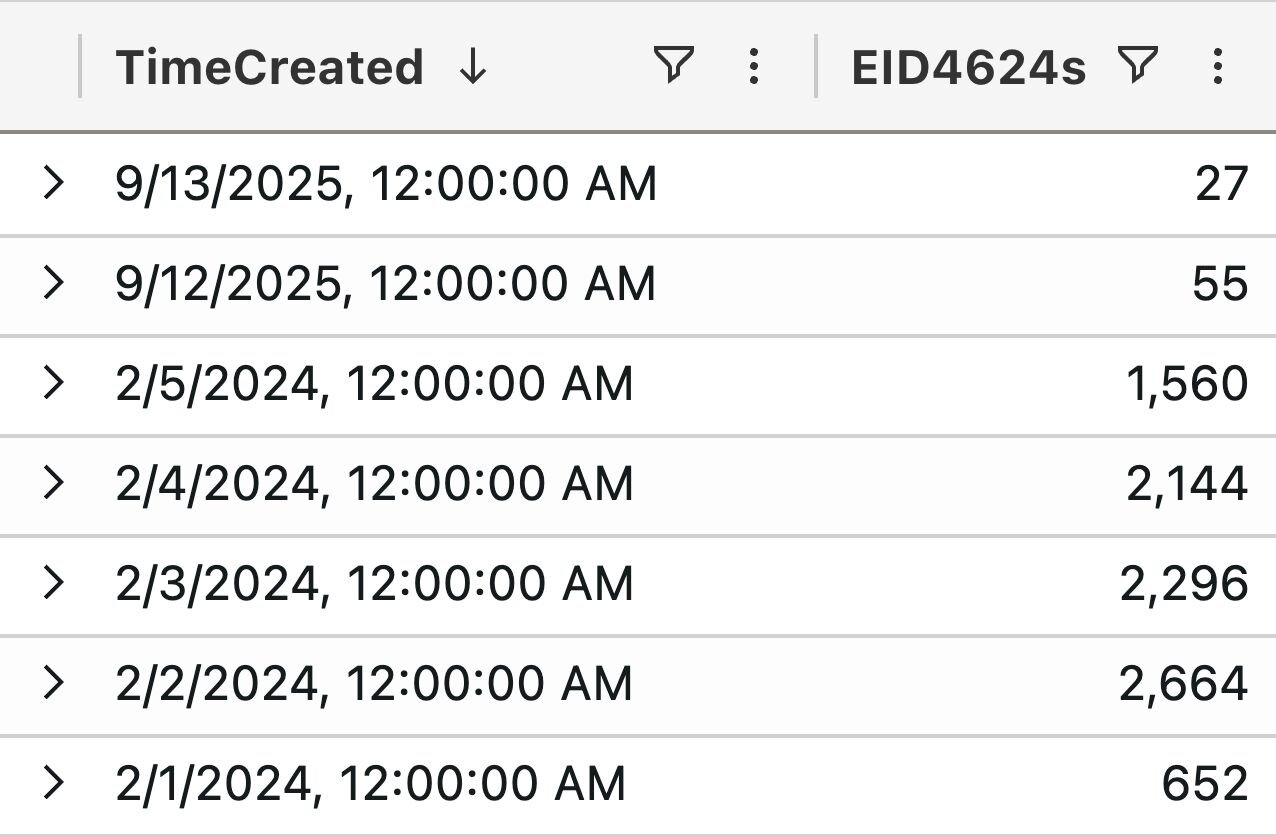
These findings are among many in a new research study analyzing over one billion CISA KEV remediation records across 10,000 organizations from 2022 through 2025. The dataset is one of the largest longitudinal studies of enterprise remediation behavior ever conducted. What it reveals is not a speed problem. It is a structural one. Vulnerability volume has surged, organizational attack surfaces have expanded faster than teams can absorb, and the percentage of critical vulnerabilities still open at Day 7 and Day 30 has worsened — not improved. Teams are working harder and falling further behind. We call it the human ceiling, and the data suggests no amount of staffing or process maturity can break through it.
Get all the findings; download the full research report.
The report introduces concepts that the industry lacked language for until now.
Average Window of Exposure (AWE) complements MTTR by capturing what it was not designed to measure: the full duration between the moment a vulnerability becomes weaponized and the moment it is remediated across the environment.
Risk Mass measures the cumulative exposure an organization absorbs while that window remains open. For a single CVE like Follina, that figure reached 33,000 exposure-days, with 80% of that exposure occurring outside the sprint that dashboards actually capture.
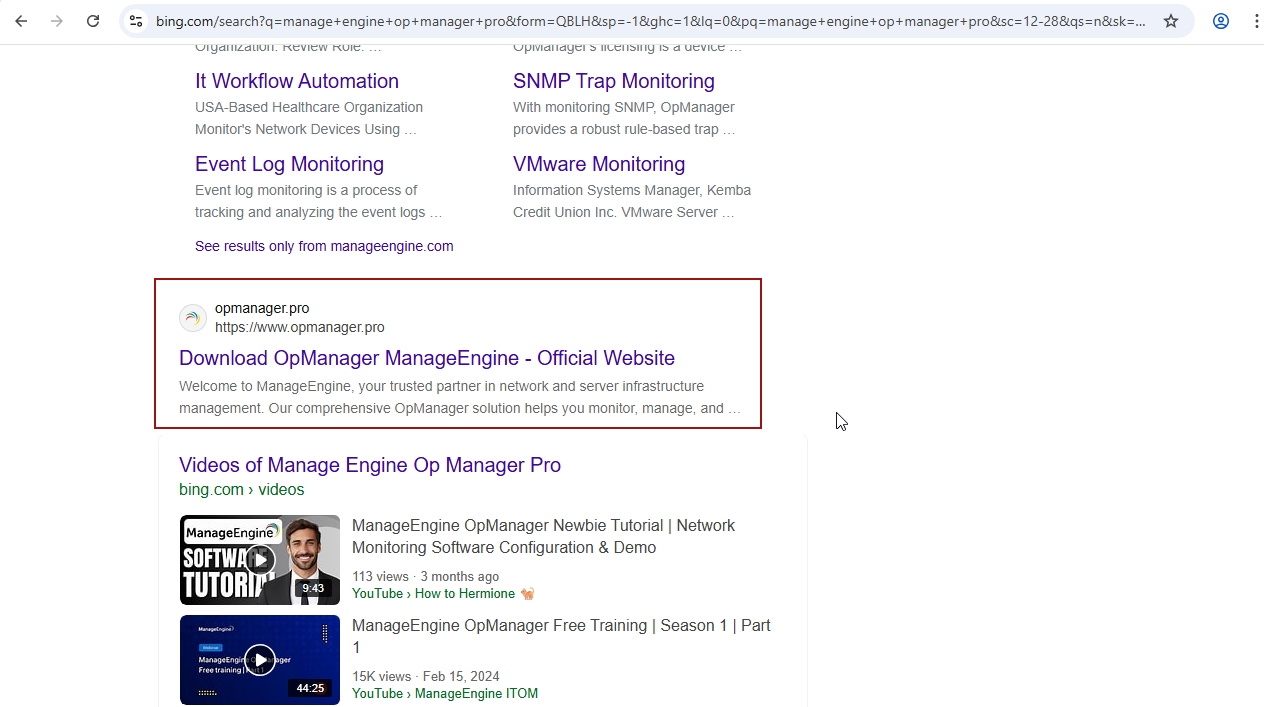
The Manual Tax quantifies the multiplier effect of the long tail—assets that manual processes cannot reach, where actual exposure runs four to five times longer than the median. And the confirmation gap reveals that even after narrowing to the sub-1% of CVEs that are weaponized and remotely exploitable, organizations still lack deterministic proof of what is actually exploitable in their environment.
The full report — The Broken Physics of Remediation — presents the evidence, introduces the metrics, and outlines the need for an approach that combines embedded intelligence to prioritize risk, active confirmation to validate threats, and automated remediation to fix fast.
Read the full report today.