TL;DR: Creating your own Bug Bounty knowledgebase (Zettelkasten for BB)

Source link
Related Articles
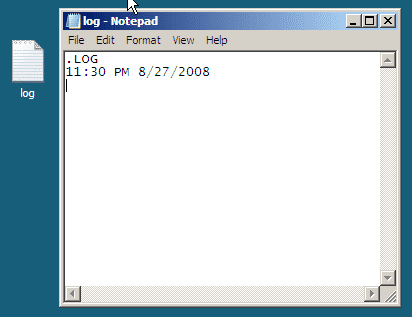
All Mix →Did You Know Notepad Could Do This?
Yeah, that Notepad. It has a feature that few know about, and I’m not talking about word wrap. You can actually use it as a…
Vulnerability Deep Dive: Gaining RCE Through ImageMagick With Frans Rosen
Table of Contents The Vulnerability ImageMagick and Related Vulnerabilities Page Description Languages PostScript GhostScript policy.xml The Exploit Script Breakdown Conclusion Sources The file upload vulnerability…
5 Minutes to Build a Basic Monitoring and Alerting System for New Subdomains
5 Minutes to Build a Basic Monitoring and Alerting System for New Subdomains Source link
How Trustpilot Manages Risk by Working with Ethical Hackers
Table of Contents Hackers Assess Real-World Product Risk Combining Continuous and Point-in-Time Assessments Maximizing the Value of Reported Vulnerabilities Tips for Getting Started with Bug…
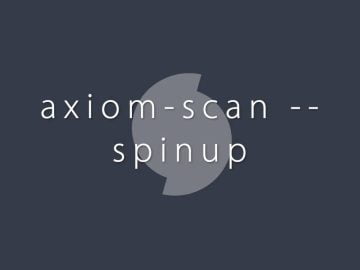
Axiom Scan New Spin Up Options with Whois Module – Apple Passive Recon
Axiom Scan New Spin Up Options with Whois Module – Apple Passive Recon Source link
Impostor Syndrome and How we Talk about it in Infosec
Impostor Syndrome and How we Talk about it in Infosec Source link