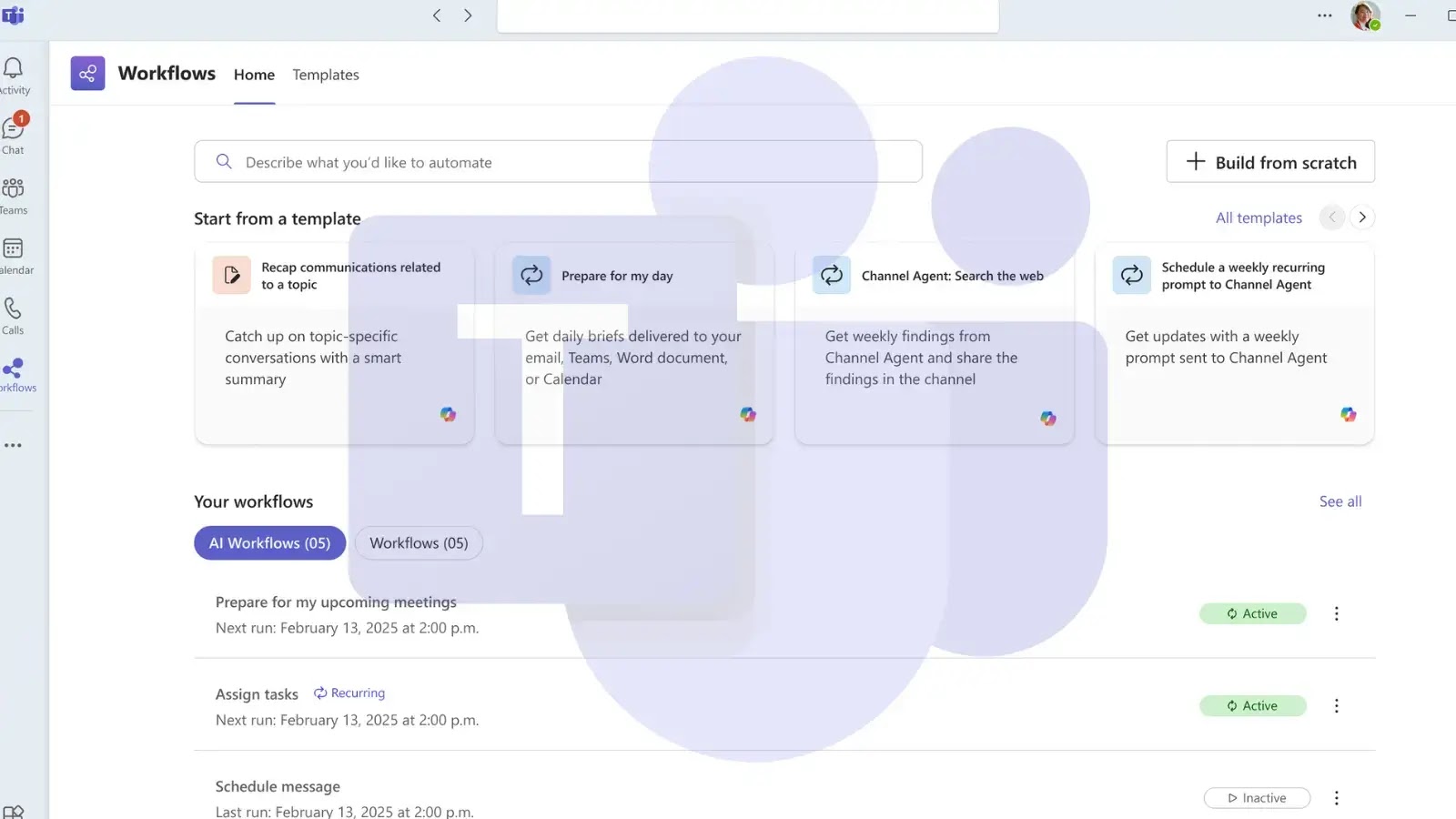
Microsoft Teams Leverages AI Workflows with Microsoft 365 Copilot for Task Automation
Microsoft is rolling out AI Workflows in the Teams Workflows app, bringing intelligent automation capabilities powered by Microsoft 365 Copilot to help users streamline daily…