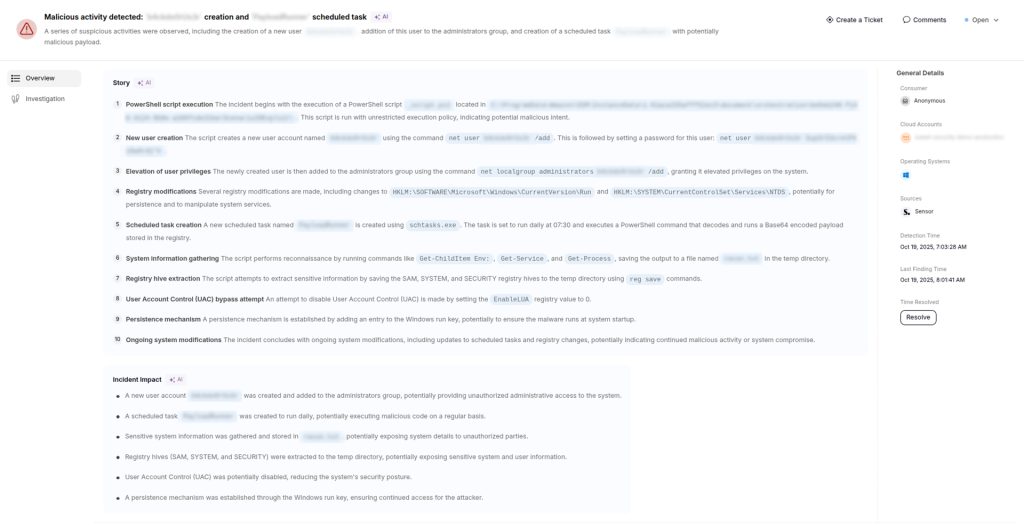
Grafana Labs says an attacker gained access to part of its GitHub environment after obtaining a compromised token, allowing the threat actor to download the company’s codebase. The open source analytics and visualization company disclosed the incident in a series of posts on X (formerly Twitter), adding that its investigation has not found evidence of customer data exposure or impact to customer systems.
The good news is that rather than resolving the matter behind closed doors, the company confirmed that the attacker later attempted to extort Grafana Labs by demanding payment in exchange for not releasing the stolen code.
According to Grafana, the company moved quickly after identifying the unauthorized access by launching a forensic investigation, invalidating the compromised credentials, and adding new safeguards around the affected environment. Grafana also said investigators believe they have identified how the credentials were exposed in the first place.
Even with source code involved, Grafana stressed that the incident did not reach customer environments. The company said its review found no signs that customer data or personal information had been accessed during the breach, and no evidence that customer operations were affected.
The decision not to pay the attacker was another part of the company’s public statement. Grafana cited long-standing FBI guidance, which warns that ransom payments do not guarantee stolen data will be recovered or kept private. The agency has repeatedly argued that paying extortion demands encourages more attacks by giving cybercriminals a financial incentive.
This decision also stands in contrast to a recent incident involving Canvas LMS parent company Instructure, which reportedly paid the ShinyHunters hacker group an undisclosed ransom amount after attackers breached its LMS portal and posted a page threatening to leak student data.
Nevertheless, source code-related breaches can still create long-term security concerns, even when customer data is untouched. Attackers sometimes study stolen code to look for undisclosed vulnerabilities, authentication logic, or deployment details that could help in future attacks.
For now, Grafana says the compromised credentials have been revoked, and additional protections are in place. The company added that it plans to release more details after its post-incident review is complete.