How They Got Hacked Episode Fifty Four 54

Source link
Related Articles
All Mix →Cybersecurity from an overhead cost to a business enabler
Table of Contents Gain a competitive edge with cybersecurity and acquire bigger accounts. Know your third-party applications and their security status. Develop faster. Stay Agile…
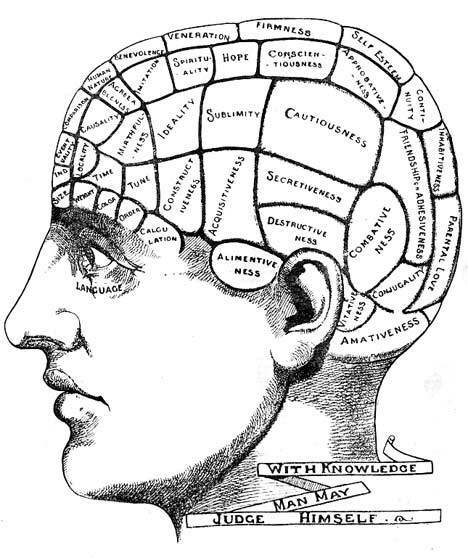
One’s Belief in Free Will Defines His Politics
I write a lot about free will, and people don’t understand why. I’ll try here again to explain. Simply, one’s stance on whether or not we…
Finding Bugs With Nuclei: Templates, Resources, and Tools
Table of Contents Table of Contents Templates Resources Tools Nuclei scans stuff for vulnerabilities. What does it scan? Modern applications, infrastructure, cloud platforms, and networks.…
How GitHub Codespaces increases productivity and lowers barriers
A look at how GitHub Codespaces can increase productivity and help new teammates and contributors start developing fast. The most recent integration between Visual Studio…
My OpenAI Event Predictions (May 2024)
Table of Contents What I anticipate All about agents A personal DA A mix of agent stuff Summary I don’t have any insider knowledge—unless you…
Webinar Recap: Attorneys Chime in on Hacker-Powered Security
Table of Contents Introduction: Legal “grey area” The Feds ? Hacker-Powered Security Start Small, But Start Now To learn more about how legal teams and…