INTERVIEW WITH @H13- : #1 BUG BOUNTY HUNTER ON SHOPIFY | METHODOLOGY, MISTAKES, TIPS & MORE…

Source link
Related Articles
All Mix →COILED SPRINGS AND JELL-O | Daniel Miessler
Table of Contents The happiest kids I know My own example So what am I getting at? It's not just the parents I think I…
Jailbreaks, Injections, and Agentic Risks
AI has officially moved out of the novelty phase. What began with people messing around with LLM-powered GenAI tools for content creation has rapidly evolved…
Why Traditional Approaches Are Failing in the AI Era — API Security
Table of Contents API Traffic is Growing in Complexity and Volume AI Agents and Automation are Complicating Matters Further Where Traditional API Security Breaks Down…
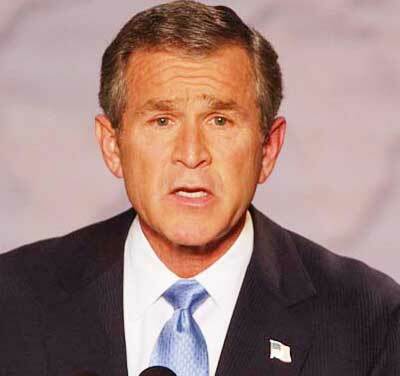
You Are Wrong About President Bush
President Bush isn’t the hateful warmonger people make him out to be. I agree that he’s hurting the United States to an obscene degree (as…
US Government Mandates Vulnerability Disclosure for IoT
This year has seen a rapid acceleration in the American government’s efforts to secure federal and state cyber infrastructure. This momentum has continued with the…
How I’d Save The United States
I’ve been experiencing growing frustration with social/political issues lately, and each time I get to thinking about various problems that this country faces, I try…