#NahamCon2022EU: Managing a Bug Bounty Program From a Hacker’s Perspective by @0xlupin

Source link
Related Articles
All Mix →OWASP TOP 10: Broken Access Control
Table of Contents Description Prevalence Potential impact Well-known events How to discover Broken Access Control How Detectify can help Exploitability Example Remediation Update: Broken Access…
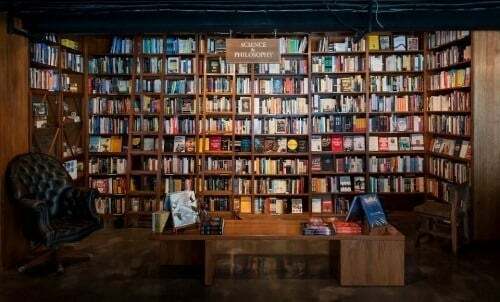
Some Thoughts on the Economic Viability of E-Books
A friend of mine (I’ll identify him if he so desires) sent me the following email: I think this is an excellent observation. My first…
The story behind HackerOne’s first anniversary gift for employees
The HackerOnesie instantly became famous the day it was introduced in 2017. Although it has been known to carry magical powers, it is now one…
Unsupervised Learning NO. 392
Unsupervised Learning is a Security, AI, and Meaning-focused podcast that looks at how best to thrive as humans in a post-AI world. It combines original…
Make Your Cybersecurity Dollars Last Longer
Table of Contents Harness AI To Do More With Less Manage Reduced Headcount Without Burning Out Staff By Effective Prioritization And Vendor Consolidation Innovate Securely…