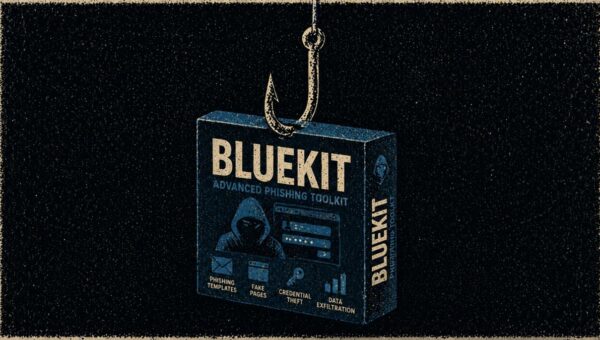
New AI-Powered Bluekit Phishing Kit Targets Major Platforms with MFA Bypass Attacks
Varonis Threat Labs has discovered a new phishing-as-a-service kit called Bluekit that is making it much easier for cyberattackers to bypass security, even when users…