A new phishing campaign uncovered in late April 2026 shows how threat actors behind the Tycoon 2FA Phishing-as-a-Service (PhaaS) kit are evolving beyond traditional credential theft.
This development comes just weeks after a global takedown effort led by Microsoft and Europol disrupted Tycoon 2FA infrastructure.
Despite that operation, the actors have quickly adapted, reusing their existing kit while shifting to a more advanced, stealthier attack method.
The attack begins with a phishing email disguised as a vendor invoice reminder. Victims are lured into clicking a Trustifi click-tracking link, which redirects through a Cloudflare Workers domain before delivering the malicious payload.
Instead of presenting a fake login page, the campaign leverages Microsoft’s legitimate device login process at microsoft.com/devicelogin.
According to eSentire’s Threat Response Unit (TRU), attackers are now abusing Microsoft’s OAuth Device Authorization Grant flow to gain access to Microsoft 365 accounts without ever collecting usernames or passwords.
Victims are instructed to enter a short “user code” displayed on a phishing page. Once entered, Microsoft handles the authentication process, including MFA.
However, by completing this step, the victim unknowingly authorizes an attacker-controlled device. This results in OAuth access and refresh tokens being issued directly to the attacker.
In simple terms, the victim is not giving away credentials they are granting access.
Tycoon 2FA Operators Use OAuth Device
TRU identified a sophisticated four-layer delivery chain that mirrors earlier Tycoon 2FA campaigns:
- Layer 1 decrypts a hidden payload in the browser using AES-GCM and obfuscated JavaScript.
- Layer 2 performs anti-analysis checks, including sandbox detection, debugger traps, and ASN-based filtering against over 230 vendors.
- Layer 3 displays a fake Microsoft CAPTCHA (“HumanCheck”) and queries a “Check Domain” to decide whether to show the phishing lure or a benign decoy site.
- Layer 4 delivers the OAuth device-code phishing page, guiding the user through the login process.
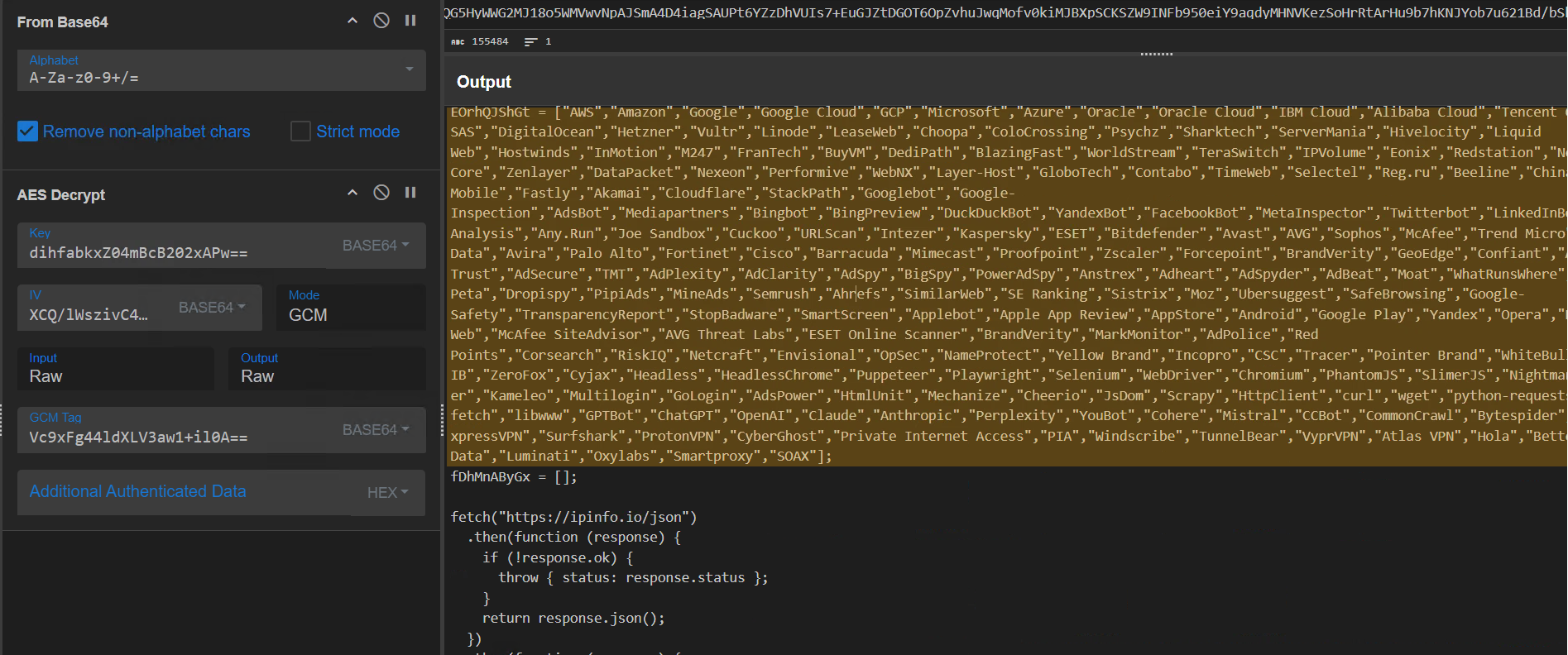
Notably, the kit retains key fingerprints from earlier versions, including CryptoJS AES-CBC encryption with a hardcoded key “1234567890123456,” consistent anti-debugging logic, and the same Check Domain architecture.
The attackers impersonate Microsoft Authentication Broker, a legitimate first-party application (AppId: 29d9ed98-a469-4536-ade2-f981bc1d605e).
Because this app is trusted, the consent prompt appears legitimate and avoids triggering typical OAuth security warnings.
Once consent is granted, attackers gain access to multiple services, including Exchange Online, Microsoft Graph, and OneDrive. A single approval effectively compromises the entire Microsoft 365 environment.
Telemetry shows attacker infrastructure hosted on Alibaba Cloud (AS45102), with automation driven by Node.js tools using “node” and “undici” user-agent strings new indicators compared to earlier axios-based activity.
This attack does not bypass MFA in the traditional sense. Instead, it exploits how OAuth device code flows work. Since authentication occurs on Microsoft’s real platform, MFA is successfully completed but for the wrong session.
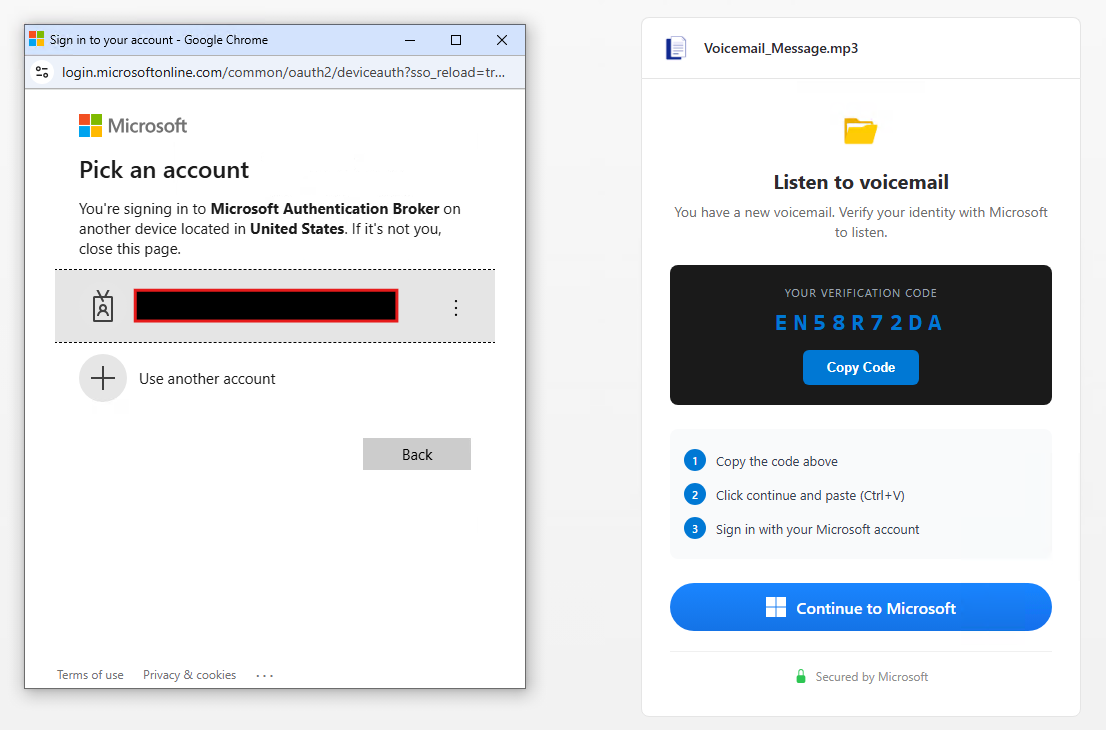
For example, a user approving a login prompt believes they are accessing a voicemail message. In reality, they are authorizing persistent access for an attacker’s device.
Security teams should monitor for unusual device-code authentication events and suspicious user-agent strings such as “node” or “undici” in Entra logs.
The reuse of Tycoon 2FA infrastructure patterns like Check Domain URLs and AES encryption routines also provides reliable detection opportunities.
To mitigate this threat, organizations should:
- Restrict or turn off OAuth device code flows for standard users.
- Enforce strict application consent policies.
- Enable Continuous Access Evaluation (CAE) for rapid token revocation.
- Monitor for anomalous OAuth activity and post-compromise behavior.
This campaign highlights a critical shift in phishing tactics. Even strong MFA protections can be undermined when attackers manipulate legitimate authentication workflows, reinforcing the need for deeper visibility into identity and token-based attacks.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.







